MSFconsole核心命令教程
MSFconsole有许多不同的命令选项可供选择。以下是Metasploit命令的核心组合,并参考其格式。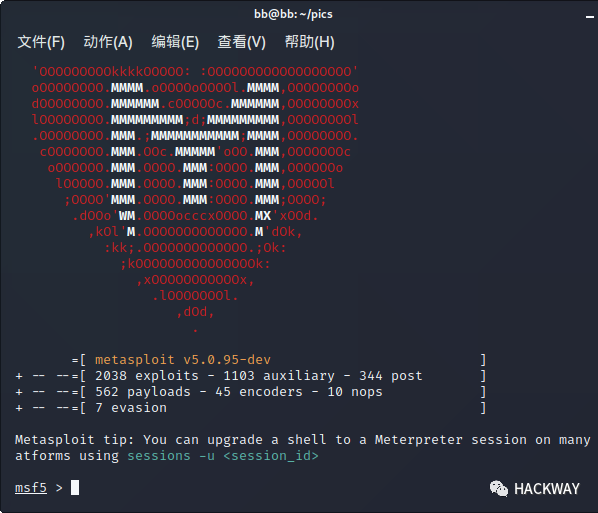
back 从当前上下文返回
banner 显示一个很棒的metasploit横幅
cd 更改当前的工作目录
color 切换颜色
connect 与主机通信
edit 使用 EDITOR编辑当前模块
exit 退出控制台
get 特定于上下文的变量的值
getg 获取全局变量的值
go_pro 启动Metasploit Web GUI
grep Grep另一个命令的输出
help 菜单
info 显示有关一个或多个模块的信息
irb 进入irb脚本模式
jobs 显示和管理工作
kill 杀死一份工作
load 加载一个框架插件
loadpath 搜索并加载路径中的模块
makerc 保存从开始到文件输入的命令
popm 将最新的模块从堆栈弹出并使其处于活动状态
previous 将之前加载的模块设置为当前模块
pushm 将活动或模块列表推入模块堆栈
quit 退出控制台
reload_all 重新加载所有定义的模块路径中的所有模块
rename_job 重命名作业
resource 运行存储在文件中的命令
route 通过会话路由流量
save 保存活动的数据存储
search 搜索模块名称和说明
sessions 转储会话列表并显示有关会话的信息
set 将特定于上下文的变量设置为一个值
setg 将全局变量设置为一个值
show 显示给定类型的模块或所有模块
sleep 在指定的秒数内不执行任何操作
spool 将控制台输出写入文件以及屏幕
threads 查看和操作后台线程
unload 卸载框架插件
unset 取消设置一个或多个特定于上下文的变量
unsetg 取消设置一个或多个全局变量
use 按名称选择模块
version 显示框架和控制台库版本号
back
一旦你完成了一个特定的模块的工作,或者你无意中选择了错误的模块,你可以发出back命令移出当前的上下文。但是,这不是必需的。就像在商用路由器中一样,您可以从其他模块中切换模块。提醒一下,变量只有在全球范围内设定后才能继续。
msf auxiliary(ms09_001_write) > backmsf >
banner
只需显示随机选择的横幅
msf > banner______________________________________________________________________________| || 3Kom SuperHack II Logon ||______________________________________________________________________________|| || || || User Name: [ security ] || || Password: [ ] || || || || [ OK ] ||______________________________________________________________________________|| || https://metasploit.com ||______________________________________________________________________________|=[ metasploit v4.16.8-dev ]+ -- --=[ 1684 exploits - 964 auxiliary - 299 post ]+ -- --=[ 498 payloads - 40 encoders - 10 nops ]+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
check
支持它的漏洞并不多,但也有一个check选项,用于检查目标是否容易受到特定漏洞攻击,而不是实际利用漏洞。
msf exploit(ms08_067_netapi) > show optionsModule options (exploit/windows/smb/ms08_067_netapi):Name Current Setting Required Description---- --------------- -------- -----------RHOST 172.16.194.134 yes The target addressRPORT 445 yes Set the SMB service portSMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC)Exploit target:Id Name-- ----0 Automatic Targetingmsf exploit(ms08_067_netapi) > check[*] Verifying vulnerable status... (path: 0x0000005a)[*] System is not vulnerable (status: 0x00000000)[*] The target is not exploitable.msf exploit(ms08_067_netapi) >
color
如果通过msfconsole获得的输出将包含颜色,则可以启用或禁用颜色输出。
msf > colorUsage: color <'true'|'false'|'auto'>Enable or disable color output.msf > color false
connect
msfconsole内置了一个微型Netcat克隆,它支持SSL,代理服务器,枢纽和文件传输。
通过使用IP地址和端口号发出connect命令,您可以像使用Netcat或Telnet一样,从msfconsole连接到远程主机。
msf > connect 192.168.1.1 23[*] Connected to 192.168.1.1:23DD-WRT v24 std (c) 2018 NewMedia-NET GmbHRelease: 04/17/18 (SVN revision: 10011)DD-WRT login:
您可以通过发出“-h”参数来查看所有附加选项。
msf > connect -h
用法
connect [选项]
描述:
与主机通信,类似于通过netcat进行交互,利用任何配置的会话透视。
选项:
-C 尝试将CRLF用于EOL序列。
-P <opt> 指定源端口。
-S <opt> 指定源地址。
-c <opt> 指定使用哪个Comm。
-h 帮助横幅。
-i <opt> 发送文件的内容。
-p <opt> 使用的代理列表。
-s 使用SSL连接。
-u 切换到UDP套接字。
-w <opt> 定连接超时。
-z 试着连接,然后返回。
edit
该edit命令将edit与 EDITOR当前模块。默认情况下,这将在Vim中打开当前模块。
msf > use exploit/windows/smb/ms10_061_spoolssmsf exploit(ms10_061_spoolss) > edit[*] Launching usr/bin/vim usr/share/metasploit-framework/modules/exploits/windows/smb/ms10_061_spoolss.rb### This module requires Metasploit: http//metasploit.com/download# Current source: https://github.com/rapid7/metasploit-framework##require 'msf/core'require 'msf/windows_error'class Metasploit3 > Msf::Exploit::RemoteRank = ExcellentRankinginclude Msf::Exploit::Remote::DCERPCinclude Msf::Exploit::Remote::SMBinclude Msf::Exploit::EXEinclude Msf::Exploit::WbemExecdef initialize(info = {})
exit
在exit命令会退出msfconsole。
msf exploit(ms10_061_spoolss) > exitroot@kali:~#
grep
该grep的命令类似的Linux的grep。它匹配来自另一个msfconsole命令输出的给定模式。
以下是使用grep从包含字符串“oracle”的模块搜索中匹配包含字符串“http”的输出的示例。
msf > grep
用法:
grep [options] pattern cmd
grep [选项] 匹配词 命令
描述:
grep控制台命令的结果(类似于Linux grep命令)
选项:
-A <opt> 显示输出的参数行匹配后。
-B <opt> 在匹配前显示输出的参数行。
-c 仅打印匹配行数。
-h 帮助横幅。
-i 忽略大小写。
-k <opt> 在输出开始处保持(包含)arg行。
-m <opt> 在arg匹配后停止。
-s <opt> 在尝试匹配之前跳过输出的arg行。
-v 反转匹配。
msf > grep http search oracleauxiliary/scanner/http/oracle_demantra_database_credentials_leak 2014-02-28 normal Oracle Demantra Database Credentials Leakauxiliary/scanner/http/oracle_demantra_file_retrieval 2014-02-28 normal Oracle Demantra Arbitrary File Retrieval with Authentication Bypassauxiliary/scanner/http/oracle_ilom_login normal Oracle ILO Manager Login Brute Force Utilityexploit/multi/http/glassfish_deployer 2011-08-04 excellent Sun/Oracle GlassFish Server Authenticated Code Executionexploit/multi/http/oracle_ats_file_upload 2016-01-20 excellent Oracle ATS Arbitrary File Uploadexploit/multi/http/oracle_reports_rce 2014-01-15 great Oracle Forms and Reports Remote Code Executionexploit/windows/http/apache_chunked 2002-06-19 good Apache Win32 Chunked Encodingexploit/windows/http/bea_weblogic_post_bof 2008-07-17 great Oracle Weblogic Apache Connector POST Request Buffer Overflowexploit/windows/http/oracle9i_xdb_pass 2003-08-18 great Oracle 9i XDB HTTP PASS Overflow (win32)exploit/windows/http/oracle_beehive_evaluation 2010-06-09 excellent Oracle BeeHive 2 voice-servlet processEvaluation() Vulnerabilityexploit/windows/http/oracle_beehive_prepareaudiotoplay 2015-11-10 excellent Oracle BeeHive 2 voice-servlet prepareAudioToPlay() Arbitrary File Uploadexploit/windows/http/oracle_btm_writetofile 2012-08-07 excellent Oracle Business Transaction Management FlashTunnelService Remote Code Executionexploit/windows/http/oracle_endeca_exec 2013-07-16 excellent Oracle Endeca Server Remote Command Executionexploit/windows/http/oracle_event_processing_upload 2014-04-21 excellent Oracle Event Processing FileUploadServlet Arbitrary File Uploadexploit/windows/http/osb_uname_jlist 2010-07-13 excellent Oracle Secure Backup Authentication Bypass/Command Injection Vulnerability
help
该help命令会给你所有可用命令的列表和小描述。
msf > help
核心命令
命令说明
? 帮助菜单
banner 显示一个很棒的metasploit横幅
cd 更改当前的工作目录
color 切换颜色
connect 与主机通信
...略...
数据库后端命令
命令说明
db_connect 连接到现有的数据库
db_disconnect 断开与当前数据库实例的连接
db_export 导出包含数据库内容的文件
db_import 导入扫描结果文件(文件类型将被自动检测)
...略...
info
该info命令将提供包括所有选项,目标和其它信息的特定模块的详细信息。请务必在使用之前始终阅读模块说明,因为有些可能会产生不希望的效果。
info命令还提供了以下信息:
作者和许可信息 漏洞引用(即:CVE,BID等) 模块可能具有的任何有效负载限制
msf > use exploit/windows/smb/ms09_050_smb2_negotiate_func_indexmsf exploit(ms09_050_smb2_negotiate_func_index) > info exploit/windows/smb/ms09_050_smb2_negotiate_func_index[-] Invalid module: infoName: MS09-050 Microsoft SRV2.SYS SMB Negotiate ProcessID Function Table DereferenceModule: exploit/windows/smb/ms09_050_smb2_negotiate_func_indexPlatform: WindowsPrivileged: YesLicense: Metasploit Framework License (BSD)Rank: GoodDisclosed: 2009-09-07Provided by:Laurent Gaffie <[[email protected]](/cdn-cgi/l/email-protection)>hdm <[[email protected]](/cdn-cgi/l/email-protection)>sf <[[email protected]](/cdn-cgi/l/email-protection)>Available targets:Id Name-- ----0 Windows Vista SP1/SP2 and Server 2008 (x86)Basic options:Name Current Setting Required Description---- --------------- -------- -----------RHOST yes The target addressRPORT 445 yes The target port (TCP)WAIT 180 yes The number of seconds to wait for the attack to complete.Payload information:Space: 1024Description:This module exploits an out of bounds function table dereference inthe SMB request validation code of the SRV2.SYS driver included withWindows Vista, Windows 7 release candidates (not RTM), and Windows2008 Server prior to R2. Windows Vista without SP1 does not seemaffected by this flaw.References:https://technet.microsoft.com/en-us/library/security/MS09-050https://cvedetails.com/cve/CVE-2009-3103/http://www.securityfocus.com/bid/36299OSVDB (57799)http://seclists.org/fulldisclosure/2009/Sep/0039.htmlhttp://www.microsoft.com/technet/security/Bulletin/MS09-050.mspxmsf exploit(ms09_050_smb2_negotiate_func_index) >
irb
运行irb命令将会让你进入一个真实的Ruby解释器shell,你可以在其中发布命令并创建Metasploit脚本。这个特性对于理解框架的内部也很有用。
msf > irb[*] Starting IRB shell...>> puts "Hello, metasploit!"Hello, metasploit!=> nil>> Framework::Version=> "4.16.8-dev"
jobs
jobs是在后台运行的模块。该jobs命令提供列出和终止这些jobs的能力。
msf > jobs -h
用法:
jobs [选项]
描述:
积极的jobs操作和交互。
选项:
-K 终止所有正在运行的作业。
-S <opt> 行搜索过滤器。
-h 帮助横幅。
-i <opt> 列出有关正在运行的作业的详细信息。
-k <opt> 按作业ID和/或范围终止作业。
-l 列出所有正在运行的作业。
-v 打印更多详细信息。与-i和-l一起使用
kill
使用jobs ID提供的kill命令将会终止任何正在运行的jobs。和linux中的kill相似;
msf exploit(ms10_002_aurora) > kill 0Stopping job: 0...[*] Server stopped.
load
该load命令加载从Metasploit工具的插件 插件目录。参数在shell上以key = val的形式传递。
msf > load
用法:
load <选项> [var=val var=val ...]
描述:
从提供的路径加载插件。
选项:
有关内置插件的列表,请执行以下操作:load -l
可选的var = val选项是可以传递给插件的自定义参数。
msf > load pcap_log[*] PcapLog plugin loaded.[*] Successfully loaded plugin: pcap_logmsf >
loadpath
该loadpath命令将加载第三部分模块树的路径,这样你可以在你的0-day,encoders(编码器),payloads(有效载荷)等成为一个Metasploit拥有更多漏洞工具集合;
msf > loadpath home/secret/modulesLoaded 0 modules.
unload
相反,unload命令会卸载先前加载的插件并删除所有扩展的命令。
msf > unload pcap_logUnloading plugin pcap_log...unloaded.
resource
该resource命令运行资源(批)可以通过msfconsole载入的文件。
msf > resource
用法:
resource path1 [path2 ...]
描述:
运行存储在提供的文件中的命令。资源文件也可能包含代码之间的ruby代码。
另见:makerc
一些攻击,如Karmetasploit,使用资源文件在运行一组命令karma.rc文件中创建的攻击。稍后,我们将讨论在Karmetasploit之外,这可能非常有用。
msf > resource karma.rc[*] Processing karma.rc for ERB directives.resource (karma.rc_.txt)> db_connect postgres:[[email protected]](/cdn-cgi/l/email-protection)/msfbookresource (karma.rc_.txt)> use auxiliary/server/browser_autopwn...略...
批处理文件可以大大加快测试和开发时间,并允许用户自动完成许多任务。除了从msfconsole加载批处理文件外,还可以使用-r标志在启动时传递它们。
下面的简单示例创建一个批处理文件,以在启动时显示Metasploit版本号。
root@kali:~# echo version > version.rcroot@kali:~# msfconsole -r version.rcIIIIII dTb.dTb _.---._II 4' v 'B .'"".'/|\`.""'.II 6. .P : .' | \ `. :II 'T;. .;P' '.' | \ `.'II 'T; ;P' `. | \ .'IIIIII 'YvP' `-.__|__.-'I love shells --egypt=[ metasploit v4.16.8-dev ]+ -- --=[ 1684 exploits - 964 auxiliary - 299 post ]+ -- --=[ 498 payloads - 40 encoders - 10 nops ]+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ][*] Processing version.rc for ERB directives.resource (version.rc)> versionFramework: 4.16.8-devConsole : 4.16.8-dev
route
Metasploit中的“route”命令允许您通过session或'comm'路由套接字,从而提供基本的旋转功能。要添加路由,请传递目标子网和网络掩码,然后传递session (comm) 号码。
msf > route -h通过提供的会话将流量发往指定的子网。
用法:
route [add/remove] subnet netmask [comm/sid]
route [add/remove] cidr [comm/sid]
route [get]
route [flush]
route [print]
子命令:
add - 制作新路线
remove - 删除路线; 'del'是一个别名
flush - 删除所有路线
get - 显示给定目标的路线
print - 显示所有活动路线
例子:
通过session 1为从192.168.0.0到192.168.0.0的所有主机添加路由
route add 192.168.0.0 255.255.255.0 1
route add 192.168.0.0/24 1
删除上述路线
route remove 192.168.0.0/24 1
route del 192.168.0.0 255.255.255.0 1
显示将用于给定主机或网络的路线
route get 192.168.0.11
meterpreter > routeNetwork routes==============Subnet Netmask Gateway------ ------- -------0.0.0.0 0.0.0.0 172.16.1.254127.0.0.0 255.0.0.0 127.0.0.1172.16.1.0 255.255.255.0 172.16.1.100172.16.1.100 255.255.255.255 127.0.0.1172.16.255.255 255.255.255.255 172.16.1.100224.0.0.0 240.0.0.0 172.16.1.100255.255.255.255 255.255.255.255 172.16.1.100
search
msfconsole包含广泛的基于正则表达式的搜索功能。如果您对所查找内容有一个大致的了解,则可以通过搜索进行搜索。在下面的输出中,正在搜索MS Bulletin MS09-011。搜索功能将在模块名称,描述,引用等内找到该字符串。
请注意,Metasploit模块的命名约定使用下划线和连字符。
msf > search usermap_scriptMatching Modules================Name Disclosure Date Rank Description---- --------------- ---- -----------exploit/multi/samba/usermap_script 2007-05-14 excellent Samba "username map script" Command Execution
help
您可以使用内置的关键字系统进一步优化您的搜索。
msf > help search
用法:
search [关键字]
关键词:
app:客户端或服务器攻击的模块
author:这个作者写的模块
bid:具有匹配的Bugtraq ID的模块
cve:具有匹配CVE ID的模块
edb:具有匹配的Exploit-DB ID的模块
name:具有匹配描述性名称的模块
platform:影响这个平台的模块
ref:具有匹配参考的模块
type:特定类型的模块(exploit,auxiliary或post)
例子:
search cve:2009 type:exploit app:client
name
要使用描述性名称进行搜索,请使用name关键字。
msf > search name:mysqlMatching Modules================Name Disclosure Date Rank Description---- --------------- ---- -----------auxiliary/admin/mysql/mysql_enum normal MySQL Enumeration Moduleauxiliary/admin/mysql/mysql_sql normal MySQL SQL Generic Queryauxiliary/analyze/jtr_mysql_fast normal John the Ripper MySQL Password Cracker (Fast Mode)auxiliary/scanner/mysql/mysql_authbypass_hashdump 2012-06-09 normal MySQL Authentication Bypass Password Dumpauxiliary/scanner/mysql/mysql_file_enum normal MYSQL File/Directory Enumeratorauxiliary/scanner/mysql/mysql_hashdump normal MYSQL Password Hashdumpauxiliary/scanner/mysql/mysql_login normal MySQL Login Utilityauxiliary/scanner/mysql/mysql_schemadump normal MYSQL Schema Dumpauxiliary/scanner/mysql/mysql_version normal MySQL Server Version Enumerationauxiliary/scanner/mysql/mysql_writable_dirs normal MYSQL Directory Write Testauxiliary/server/capture/mysql normal Authentication Capture: MySQLexploit/linux/mysql/mysql_yassl_getname 2010-01-25 good MySQL yaSSL CertDecoder::GetName Buffer Overflowexploit/linux/mysql/mysql_yassl_hello 2008-01-04 good MySQL yaSSL SSL Hello Message Buffer Overflowexploit/windows/mysql/mysql_mof 2012-12-01 excellent Oracle MySQL for Microsoft Windows MOF Executionexploit/windows/mysql/mysql_payload 2009-01-16 excellent Oracle MySQL for Microsoft Windows Payload Executionexploit/windows/mysql/mysql_start_up 2012-12-01 excellent Oracle MySQL for Microsoft Windows FILE Privilege Abuseexploit/windows/mysql/mysql_yassl_hello 2008-01-04 average MySQL yaSSL SSL Hello Message Buffer Overflowexploit/windows/mysql/scrutinizer_upload_exec 2012-07-27 excellent Plixer Scrutinizer NetFlow and sFlow Analyzer 9 Default MySQL Credential
platform
您可以使用platform将搜索范围缩小到影响特定platform(平台)的模块。
msf > search platform:aixMatching Modules================Name Disclosure Date Rank Description---- --------------- ---- -----------exploit/aix/local/ibstat_path 2013-09-24 excellent ibstat $PATH Privilege Escalationexploit/aix/rpc_cmsd_opcode21 2009-10-07 great AIX Calendar Manager Service Daemon (rpc.cmsd) Opcode 21 Buffer Overflowexploit/aix/rpc_ttdbserverd_realpath 2009-06-17 great ToolTalk rpc.ttdbserverd _tt_internal_realpath Buffer Overflow (AIX)payload/aix/ppc/shell_bind_tcp normal AIX Command Shell, Bind TCP Inlinepayload/aix/ppc/shell_find_port normal AIX Command Shell, Find Port Inlinepayload/aix/ppc/shell_interact normal AIX execve Shell for inetdpayload/aix/ppc/shell_reverse_tcp normal AIX Command Shell, Reverse TCP Inlinepost/aix/hashdump normal AIX Gather Dump Password Hashespost/multi/manage/sudo normal Multiple Linux Unix Post Sudo Upgrade Shellpost/multi/recon/local_exploit_suggester normal Multi Recon Local Exploit Suggester
type
使用该type可以按模块类型进行过滤,如auxiliary(辅助),post(提交),exploit(利用)等。
msf > search type:postMatching Modules================Name Disclosure Date Rank Description---- --------------- ---- -----------post/linux/gather/checkvm normal Linux Gather Virtual Environment Detectionpost/linux/gather/enum_cron normal Linux Cron Job Enumerationpost/linux/gather/enum_linux normal Linux Gather System Information...略...
author
使用author关键字搜索可让您搜索您最喜爱的作者的模块。
msf > search author:dookieMatching Modules================Name Disclosure Date Rank Description---- --------------- ---- -----------exploit/osx/http/evocam_webserver 2010-06-01 average MacOS X EvoCam HTTP GET Buffer Overflowexploit/osx/misc/ufo_ai 2009-10-28 average UFO: Alien Invasion IRC Client Buffer Overflowexploit/windows/browser/amaya_bdo 2009-01-28 normal Amaya Browser v11.0 'bdo' Tag Overflowexploit/windows/browser/communicrypt_mail_activex 2010-05-19 great CommuniCrypt Mail 1.16 SMTP ActiveX Stack Buffer Overflowexploit/windows/browser/mozilla_reduceright 2011-06-21 normal Mozilla Firefox Array.reduceRight() Integer Overflowexploit/windows/browser/nctaudiofile2_setformatlikesample 2007-01-24 normal NCTAudioFile2 v2.x ActiveX Control SetFormatLikeSample() Buffer Overflowexploit/windows/fileformat/a_pdf_wav_to_mp3 2010-08-17 normal A-PDF WAV to MP3 v1.0.0 Buffer Overflowexploit/windows/fileformat/adobe_illustrator_v14_eps 2009-12-03 great Adobe Illustrator CS4 v14.0.0exploit/windows/fileformat/audio_wkstn_pls 2009-12-08 good Audio Workstation 6.4.2.4.3 pls Buffer Overflowexploit/windows/fileformat/audiotran_pls 2010-01-09 good Audiotran 1.4.1 (PLS File) Stack Buffer Overflowexploit/windows/fileformat/fatplayer_wav 2010-10-18 normal Fat Player Media Player 0.6b0 Buffer Overflowexploit/windows/fileformat/feeddemon_opml 2009-02-09 great FeedDemon Stack Buffer Overflowexploit/windows/fileformat/foxit_title_bof 2010-11-13 great Foxit PDF Reader v4.1.1 Title Stack Buffer Overflowexploit/windows/fileformat/ideal_migration_ipj 2009-12-05 great PointDev IDEAL Migration Buffer Overflowexploit/windows/fileformat/millenium_mp3_pls 2009-07-30 great Millenium MP3 Studio 2.0 (PLS File) Stack Buffer Overflowexploit/windows/fileformat/somplplayer_m3u 2010-01-22 great S.O.M.P.L 1.0 Player Buffer Overflowexploit/windows/fileformat/varicad_dwb 2010-03-17 great VariCAD 2010-2.05 EN (DWB File) Stack Buffer Overflowexploit/windows/fileformat/wm_downloader_m3u 2010-07-28 normal WM Downloader 3.1.2.2 Buffer Overflowexploit/windows/ftp/trellian_client_pasv 2010-04-11 normal Trellian FTP Client 3.01 PASV Remote Buffer Overflowexploit/windows/ftp/xftp_client_pwd 2010-04-22 normal Xftp FTP Client 3.0 PWD Remote Buffer Overflowexploit/windows/misc/eureka_mail_err 2009-10-22 normal Eureka Email 2.2q ERR Remote Buffer Overflowexploit/windows/misc/hp_omniinet_4 2011-06-29 good HP OmniInet.exe Opcode 20 Buffer Overflowexploit/windows/misc/nettransport 2010-01-02 normal NetTransport Download Manager 2.90.510 Buffer Overflowexploit/windows/misc/ufo_ai 2009-10-28 average UFO: Alien Invasion IRC Client Buffer Overflow
multiple
您还可以将multiple关键字组合在一起以进一步缩小返回的结果。
msf > search cve:2011 author:jduck platform:linuxMatching Modules================Name Disclosure Date Rank Description---- --------------- ---- -----------exploit/linux/misc/netsupport_manager_agent 2011-01-08 average NetSupport Manager Agent Remote Buffer Overflow
sessions
该sessions命令可以列出,互动,并杀死催生了sessions。sessions可以是shell,Meterpreter会话,VNC等。
msf > sessions -h
用法:
sessions [选项] 或 sessions [ID]
描述:
活动的会话操作和交互。
选项:
-C <opt> 对使用-i或全部给定的会话运行Meterpreter命令
-K 终止所有会话
-c <opt> 在由-i或全部给定的会话上运行命令
-h 帮助横幅
-i <opt> 与提供的会话ID进行交互
-k <opt> 按会话ID和/或范围终止会话
-l 列出所有活动会话
-q 安静模式
-r 重置用-i或全部给定的会话的环形缓冲区
-s <opt> 在与-i或全部给定的会话上运行脚本
-t <opt> 设置响应超时(默认值:15)
-u <opt> 在许多平台上将shell升级到meterpreter会话
-v 以详细模式列出会话
-x 在会话表中显示扩展信息
许多选项允许使用逗号和破折号指定会话范围。
例如:
sessions -s checkvm -i 1,3-5 或者 sessions -k 1-2,5,6
要列出任何活动会话,请将 **-l **选项传递给sessions。
msf exploit(3proxy) > sessions -lActive sessions===============Id Description Tunnel-- ----------- ------1 Command shell 192.168.1.101:33191 -> 192.168.1.104:4444
要与给定的会话进行交互,只需使用' **-i **'开关,然后使用sessions的Id号码。
msf exploit(3proxy) > sessions -i 1[*] Starting interaction with 1...C:WINDOWSsystem32>
set
该set命令允许您配置框架选项和参数为你正在使用的当前模块。
msf auxiliary(ms09_050_smb2_negotiate_func_index) > set RHOST 172.16.194.134RHOST => 172.16.194.134msf auxiliary(ms09_050_smb2_negotiate_func_index) > show optionsModule options (exploit/windows/smb/ms09_050_smb2_negotiate_func_index):Name Current Setting Required Description---- --------------- -------- -----------RHOST 172.16.194.134 yes The target addressRPORT 445 yes The target portWAIT 180 yes The number of seconds to wait for the attack to complete.Exploit target:Id Name-- ----0 Windows Vista SP1/SP2 and Server 2008 (x86)
Metasploit还允许您设置“encoder(编码器)”以在运行时使用。如果您不确定哪种“payload(有效负载”)编码方法适用于给定的漏洞攻击,那么这对于攻击开发尤其有用。
msf exploit(ms09_050_smb2_negotiate_func_index) > show encodersCompatible Encoders===================Name Disclosure Date Rank Description---- --------------- ---- -----------generic/eicar manual The EICAR Encodergeneric/none normal The "none" Encoderx86/add_sub manual Add/Sub Encoderx86/alpha_mixed low Alpha2 Alphanumeric Mixedcase Encoderx86/alpha_upper low Alpha2 Alphanumeric Uppercase Encoderx86/avoid_underscore_tolower manual Avoid underscore/tolowerx86/avoid_utf8_tolower manual Avoid UTF8/tolowerx86/bloxor manual BloXor - A Metamorphic Block Based XOR Encoderx86/bmp_polyglot manual BMP Polyglotx86/call4_dword_xor normal Call+4 Dword XOR Encoderx86/context_cpuid manual CPUID-based Context Keyed Payload Encoderx86/context_stat manual stat(2)-based Context Keyed Payload Encoderx86/context_time manual time(2)-based Context Keyed Payload Encoderx86/countdown normal Single-byte XOR Countdown Encoderx86/fnstenv_mov normal Variable-length Fnstenv/mov Dword XOR Encoderx86/jmp_call_additive normal Jump/Call XOR Additive Feedback Encoderx86/nonalpha low Non-Alpha Encoderx86/nonupper low Non-Upper Encoderx86/opt_sub manual Sub Encoder (optimised)x86/service manual Register Servicex86/shikata_ga_nai excellent Polymorphic XOR Additive Feedback Encoderx86/single_static_bit manual Single Static Bitx86/unicode_mixed manual Alpha2 Alphanumeric Unicode Mixedcase Encoderx86/unicode_upper manual Alpha2 Alphanumeric Unicode Uppercase Encoder
unset
当然,set命令的相反部分是unset的。unset会删除以前使用set进行配置的参数。您可以全部取消全部删除所有分配的变量。
msf > set RHOSTS 192.168.1.0/24RHOSTS => 192.168.1.0/24msf > set THREADS 50THREADS => 50msf > setGlobal======Name Value---- -----RHOSTS 192.168.1.0/24THREADS 50msf > unset THREADSUnsetting THREADS...msf > unset allFlushing datastore...msf > setGlobal======No entries in data store.
setg
为了在pentest中节省大量输入,可以在msfconsole中设置全局变量。你可以用setg命令来做到这一点。一旦这些设置完成,您就可以在任意多个漏洞利用和辅助模块中使用它们。您也可以将它们保存下次启动msfconsole时使用。然而,陷阱是忘记了你已经保存了全局变量,所以在运行或利用之前总是检查你的选项。相反,您可以使用unsetg命令取消设置全局变量。在下面的例子中,变量以全部大写形式输入(即:LHOST),但Metasploit不区分大小写,因此没有必要这样做。
msf> setg LHOST 192.168.1.101LHOST => 192.168.1.101msf> setg RHOSTS 192.168.1.0/24RHOSTS => 192.168.1.0/24msf> setg RHOST 192.168.1.136RHOST => 192.168.1.136
设置完不同的变量后,您可以运行save命令来保存当前的环境和设置。保存设置后,它们将在启动时自动加载,这样就不必再次设置所有内容。
msf > saveSaved configuration to: /root/.msf4/configmsf >
show
在msfconsole提示符下输入show会显示Metasploit中的每个模块。
msf > showEncoders========Name Disclosure Date Rank Description---- --------------- ---- -----------cmd/generic_sh good Generic Shell Variable Substitution Command Encodercmd/ifs low Generic ${IFS} Substitution Command Encodercmd/printf_php_mq manual printf(1) via PHP magic_quotes Utility Command Encoder...略...
您可以使用许多show命令,但您最常使用的命令是:show auxiliary, show exploits, show payloads, show encoders 和 **show nops **.
auxiliary
执行show exploits将显示Metasploit中所有可用辅助模块的列表。如前所述,辅助模块包括扫描器,拒绝服务模块,模糊器等。
msf > show auxiliaryAuxiliary=========Name Disclosure Date Rank Description---- --------------- ---- -----------admin/2wire/xslt_password_reset 2007-08-15 normal 2Wire Cross-Site Request Forgery Password Reset Vulnerabilityadmin/backupexec/dump normal Veritas Backup Exec Windows Remote File Accessadmin/backupexec/registry normal Veritas Backup Exec Server Registry Access...略...
exploits
自然,显示“exploits(漏洞利用)”将是你最感兴趣的命令,因为Metasploit的核心是关于漏洞。运行显示漏洞获取框架中包含的所有漏洞列表。
msf > show exploitsExploits========Name Disclosure Date Rank Description---- --------------- ---- -----------aix/rpc_cmsd_opcode21 2009-10-07 great AIX Calendar Manager Service Daemon (rpc.cmsd) Opcode 21 Buffer Overflowaix/rpc_ttdbserverd_realpath 2009-06-17 great ToolTalk rpc.ttdbserverd _tt_internal_realpath Buffer Overflow (AIX)bsdi/softcart/mercantec_softcart 2004-08-19 great Mercantec SoftCart CGI Overflow...略...
MSFconsole Payloads
运行显示Payloads将显示Metasploit中所有可用平台的所有不同Payloads。
msf > show payloadsPayloads========Name Disclosure Date Rank Description---- --------------- ---- -----------aix/ppc/shell_bind_tcp normal AIX Command Shell, Bind TCP Inlineaix/ppc/shell_find_port normal AIX Command Shell, Find Port Inlineaix/ppc/shell_interact normal AIX execve shell for inetd...略...
payloads
正如你所看到的,有很多可用的payloads。幸运的是,当您处于特定漏洞利用的模块时,运行的show payload将仅显示与该漏洞兼容的payloads。
例如,如果它是Windows漏洞利用,则不会显示Linux的“payloads(有效负载)”。
msf exploit(ms08_067_netapi) > show payloadsCompatible Payloads===================Name Disclosure Date Rank Description---- --------------- ---- -----------generic/custom normal Custom Payloadgeneric/debug_trap normal Generic x86 Debug Trapgeneric/shell_bind_tcp normal Generic Command Shell, Bind TCP Inline...略...
options
如果您选择了特定模块,则可以发出show options命令来显示该特定模块可用和/或必需的设置。
msf exploit(ms08_067_netapi) > show optionsModule options:Name Current Setting Required Description---- --------------- -------- -----------RHOST yes The target addressRPORT 445 yes Set the SMB service portSMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC)Exploit target:Id Name-- ----0 Automatic Targeting
targets
如果您不确定操作系统是否容易受到特定漏洞攻击,请在漏洞利用模块的上下文中运行show targets命令以查看哪些目标受支持。
msf exploit(ms08_067_netapi) > show targetsExploit targets:Id Name-- ----0 Automatic Targeting1 Windows 2000 Universal10 Windows 2003 SP1 Japanese (NO NX)11 Windows 2003 SP2 English (NO NX)12 Windows 2003 SP2 English (NX)...略...
advanced
如果您希望进一步微调漏洞,可以通过运行show advanced来查看更多高级选项。
msf exploit(ms08_067_netapi) > show advancedModule advanced options (exploit/windows/smb/ms08_067_netapi):Name Current Setting Required Description---- --------------- -------- -----------CHOST no The local client addressCPORT no The local client portConnectTimeout 10 yes Maximum number of seconds to establish a TCP connectionContextInformationFile no The information file that contains context informationDCERPC::ReadTimeout 10 yes The number of seconds to wait for DCERPC responsesDisablePayloadHandler false no Disable the handler code for the selected payloadEnableContextEncoding false no Use transient context when encoding payloadsNTLM::SendLM true yes Always send the LANMAN response (except when NTLMv2_session is specified)NTLM::SendNTLM true yes Activate the 'Negotiate NTLM key' flag, indicating the use of NTLM responsesNTLM::SendSPN true yes Send an avp of type SPN in the ntlmv2 client blob, this allows authentication on Windows 7+/Server 2008 R2+ when SPN is requiredNTLM::UseLMKey false yes Activate the 'Negotiate Lan Manager Key' flag, using the LM key when the LM response is sentNTLM::UseNTLM2_session true yes Activate the 'Negotiate NTLM2 key' flag, forcing the use of a NTLMv2_sessionNTLM::UseNTLMv2 true yes Use NTLMv2 instead of NTLM2_session when 'Negotiate NTLM2' key is trueProxies no A proxy chain of format type:host:port[,type:host:port][...]SMB::ChunkSize 500 yes The chunk size for SMB segments, bigger values will increase speed but break NT 4.0 and SMB signingSMB::Native_LM Windows 2000 5.0 yes The Native LM to send during authenticationSMB::Native_OS Windows 2000 2195 yes The Native OS to send during authenticationSMB::VerifySignature false yes Enforces client-side verification of server response signaturesSMBDirect true no The target port is a raw SMB service (not NetBIOS)SMBDomain . no The Windows domain to use for authenticationSMBName *SMBSERVER yes The NetBIOS hostname (required for port 139 connections)SMBPass no The password for the specified usernameSMBUser no The username to authenticate asSSL false no Negotiate SSL/TLS for outgoing connectionsSSLCipher no String for SSL cipher - "DHE-RSA-AES256-SHA" or "ADH"SSLVerifyMode PEER no SSL verification method (Accepted: CLIENT_ONCE, FAIL_IF_NO_PEER_CERT, NONE, PEER)SSLVersion Auto no Specify the version of SSL/TLS to be used (Auto, TLS and SSL23 are auto-negotiate) (Accepted: Auto, SSL2, SSL3, SSL23, TLS, TLS1, TLS1.1, TLS1.2)VERBOSE false no Enable detailed status messagesWORKSPACE no Specify the workspace for this moduleWfsDelay 0 no Additional delay when waiting for a session
encoders
正在运行show encoders将显示MSF中可用“encoders(编码器)”的列表。
msf > show encodersEncoders========Name Disclosure Date Rank Description---- --------------- ---- -----------cmd/echo good Echo Command Encodercmd/generic_sh manual Generic Shell Variable Substitution Command Encodercmd/ifs low Generic ${IFS} Substitution Command Encodercmd/perl normal Perl Command Encodercmd/powershell_base64 excellent Powershell Base64 Command Encodercmd/printf_php_mq manual printf(1) via PHP magic_quotes Utility Command Encodergeneric/eicar manual The EICAR Encodergeneric/none normal The "none" Encodermipsbe/byte_xori normal Byte XORi Encodermipsbe/longxor normal XOR Encodermipsle/byte_xori normal Byte XORi Encodermipsle/longxor normal XOR Encoderphp/base64 great PHP Base64 Encoderppc/longxor normal PPC LongXOR Encoderppc/longxor_tag normal PPC LongXOR Encodersparc/longxor_tag normal SPARC DWORD XOR Encoderx64/xor normal XOR Encoderx64/zutto_dekiru manual Zutto Dekirux86/add_sub manual Add/Sub Encoderx86/alpha_mixed low Alpha2 Alphanumeric Mixedcase Encoderx86/alpha_upper low Alpha2 Alphanumeric Uppercase Encoderx86/avoid_underscore_tolower manual Avoid underscore/tolowerx86/avoid_utf8_tolower manual Avoid UTF8/tolowerx86/bloxor manual BloXor - A Metamorphic Block Based XOR Encoderx86/bmp_polyglot manual BMP Polyglotx86/call4_dword_xor normal Call+4 Dword XOR Encoderx86/context_cpuid manual CPUID-based Context Keyed Payload Encoderx86/context_stat manual stat(2)-based Context Keyed Payload Encoderx86/context_time manual time(2)-based Context Keyed Payload Encoderx86/countdown normal Single-byte XOR Countdown Encoderx86/fnstenv_mov normal Variable-length Fnstenv/mov Dword XOR Encoderx86/jmp_call_additive normal Jump/Call XOR Additive Feedback Encoderx86/nonalpha low Non-Alpha Encoderx86/nonupper low Non-Upper Encoderx86/opt_sub manual Sub Encoder (optimised)x86/service manual Register Servicex86/shikata_ga_nai excellent Polymorphic XOR Additive Feedback Encoderx86/single_static_bit manual Single Static Bitx86/unicode_mixed manual Alpha2 Alphanumeric Unicode Mixedcase Encoderx86/unicode_upper manual Alpha2 Alphanumeric Unicode Uppercase Encoder
nops
最后,运行 **show nops **命令将显示Metasploit必须提供的“NOP(空指令)”生成器。
msf > show nopsNOP Generators==============Name Disclosure Date Rank Description---- --------------- ---- -----------aarch64/simple normal Simplearmle/simple normal Simplemipsbe/better normal Betterphp/generic normal PHP Nop Generatorppc/simple normal Simplesparc/random normal SPARC NOP Generatortty/generic normal TTY Nop Generatorx64/simple normal Simplex86/opty2 normal Opty2x86/single_byte normal Single Byte
use
当您决定使用某个特定模块时,请发出use命令来选择它。在使用命令改变你的需要选择的模块,露出特定类型的命令。在下面的输出中注意,之前设置的全局变量已经被配置。
msf > use dos/windows/smb/ms09_001_writemsf auxiliary(ms09_001_write) > show optionsModule options:Name Current Setting Required Description---- --------------- -------- -----------RHOST yes The target addressRPORT 445 yes Set the SMB service portmsf auxiliary(ms09_001_write) >