Snort简介
1998年,Martin Roesch用C语言开发了开放源代码的入侵检测系统Snort。直至今天,Snort已发展成为一个具有多平台(Multi-Platform)、实时(Real-Time)流量分析、网络IP数据包(Pocket)记录等特性的强大的网络入侵检测/防御系统,即NIDS/NIPS。
Snort能够对网络上的数据包进行抓包分析,但区别于其它嗅探器的是,它能根据所定义的规则进行响应及处理。Snort 通过对获取的数据包,进行各规则的分析后,根据规则链,可采取Activation(报警并启动另外一个动态规则链)、Dynamic(由其它的规则包调用)、Alert(报警),Pass(忽略),Log(不报警但记录网络流量)五种响应的机制。
Snort有数据包嗅探,数据包分析,数据包检测,响应处理等多种功能,每个模块实现不同的功能,各模块都是用插件的方式和Snort相结合,功能扩展方便。例如,预处理插件的功能就是在规则匹配误用检测之前运行,完成TIP碎片重组,http解码,telnet解码等功能,处理插件完成检查协议各字段,关闭连接,攻击响应等功能,输出插件将得理后的各种情况以日志或警告的方式输出。
一. 安装依赖包(注意:不要换源,使用Ubuntu自带源source.list)
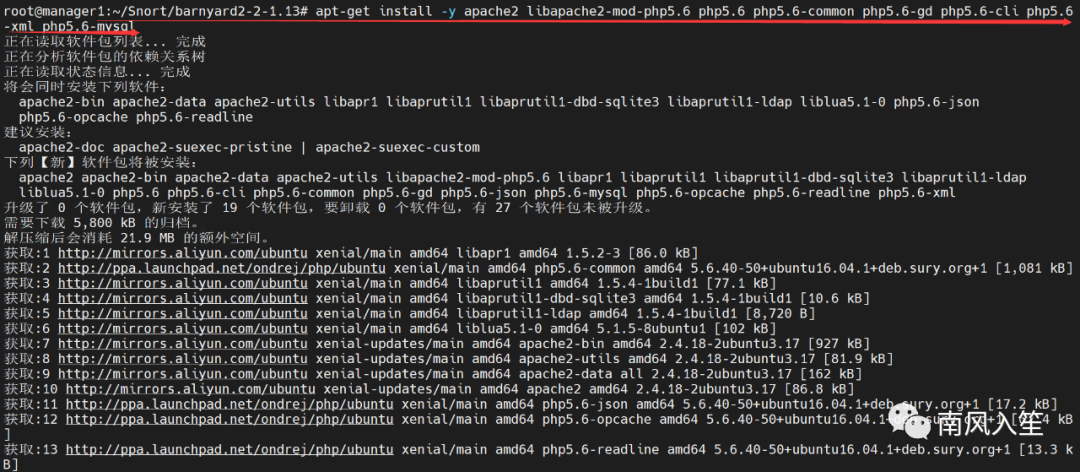
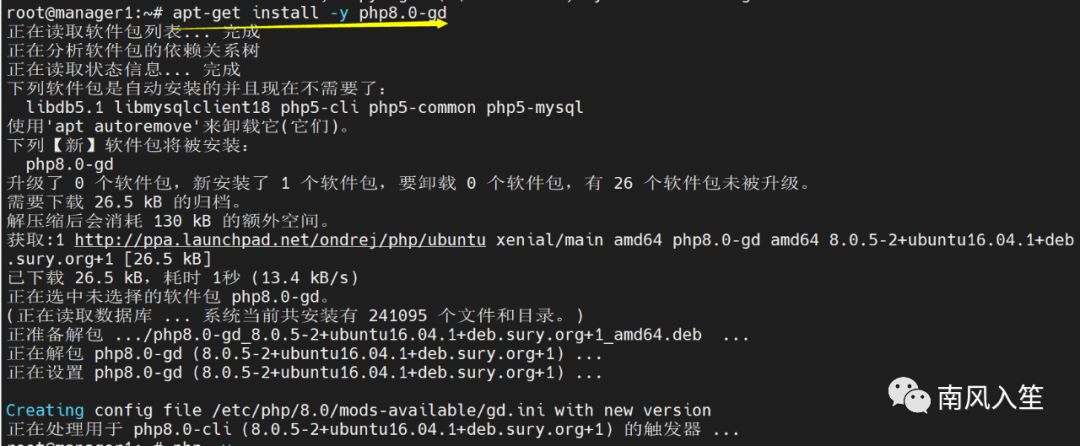
sudo apt-get update -ysudo apt-get dist-upgrade -ysudo apt-get install -y zlib1g-dev liblzma-dev openssl libssl-devsudo apt-get install -y build-essential bison flexsudo apt-get install -y libpcap-dev libpcre3-dev libdumbnet-dev libnghttp2-devsudo apt-get install -y mysql-server libmysqlclient-dev mysql-client autoconf libtoolsudo apt-get install -y libcrypt-ssleay-perl liblwp-useragent-determined-perl libwww-perlsudo add-apt-repository ppa:ondrej/phpsudo apt-get update -ysudo apt-get install -y apache2 libapache2-mod-php5.6 php5.6 php5.6-common php5.6-gd php5.6-cli php5.6-xml php5.6-mysqlsudo apt-get install -y php-pear libphp-adodb
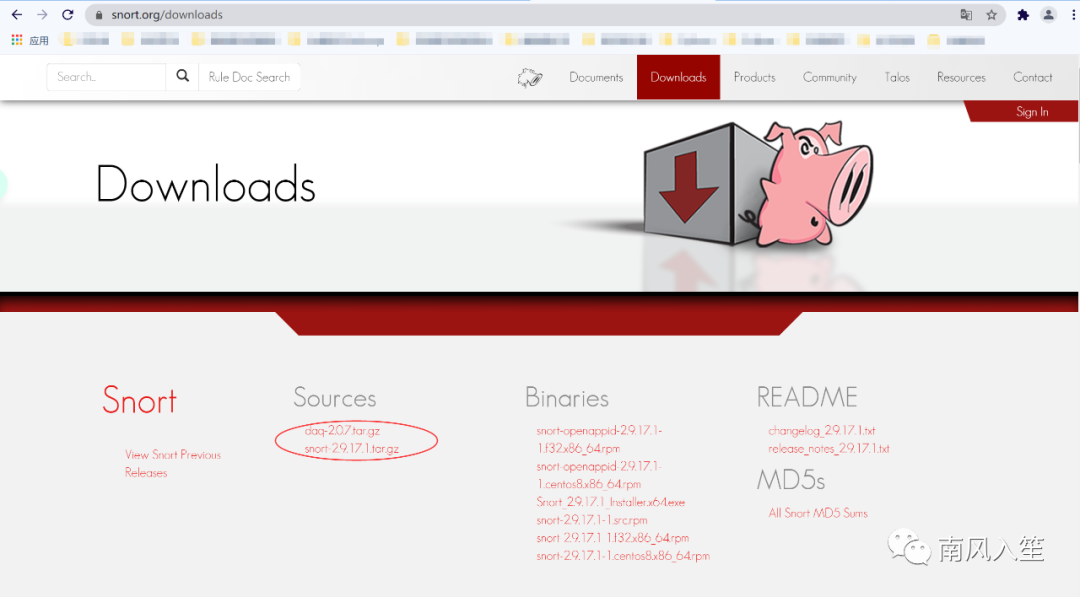
二. 下载软件
wget https://github.com/firnsy/barnyard2/archive/v2-1.13.tar.gz -O barnyard2-2-1.13.tar.gzwget https://github.com/shirkdog/pulledpork/archive/v0.7.3.tar.gz -O pulledpork-v0.7.3.tar.gzwget https://sourceforge.net/projects/adodb/files/adodb-php5-only/adodb-520-for-php5/adodb-5.20.8.tar.gzwget http://sourceforge.net/projects/secureideas/files/BASE/base-1.4.5/base-1.4.5.tar.gz注意:这四个软件如果使用命令下载,复制链接到浏览器即可下载,然后传至系统即可。
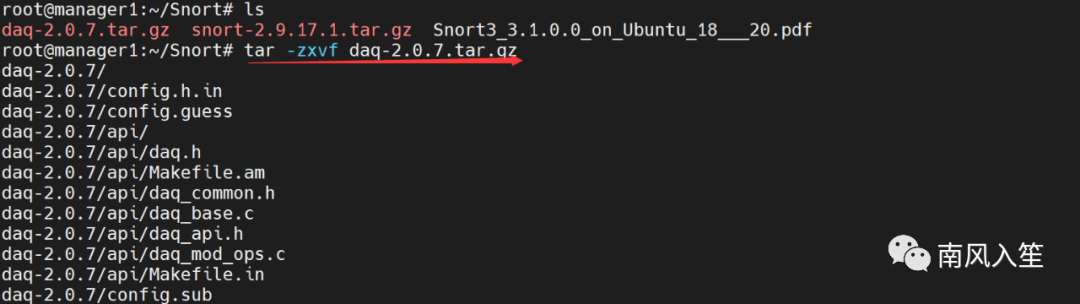
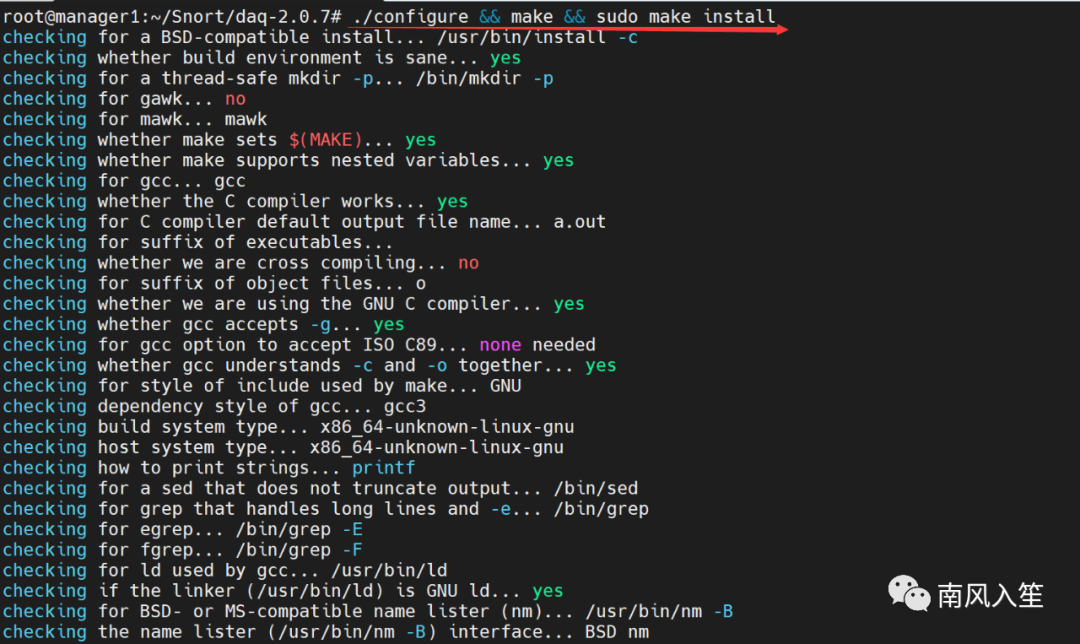
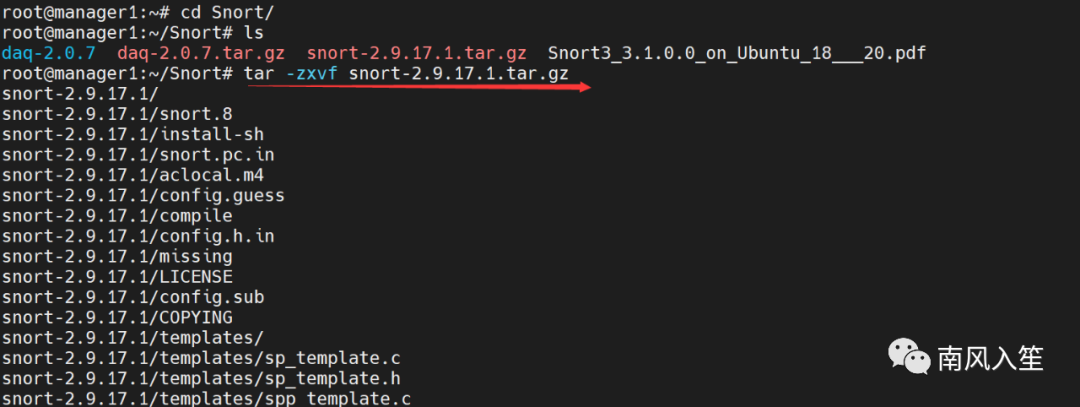
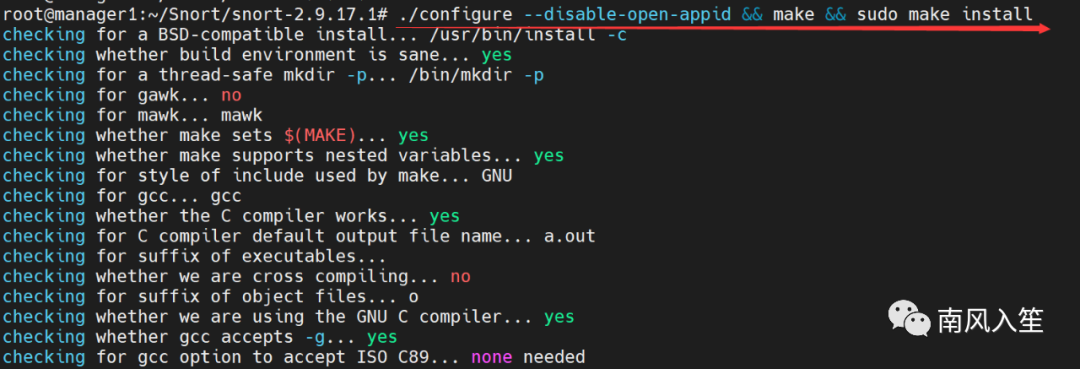
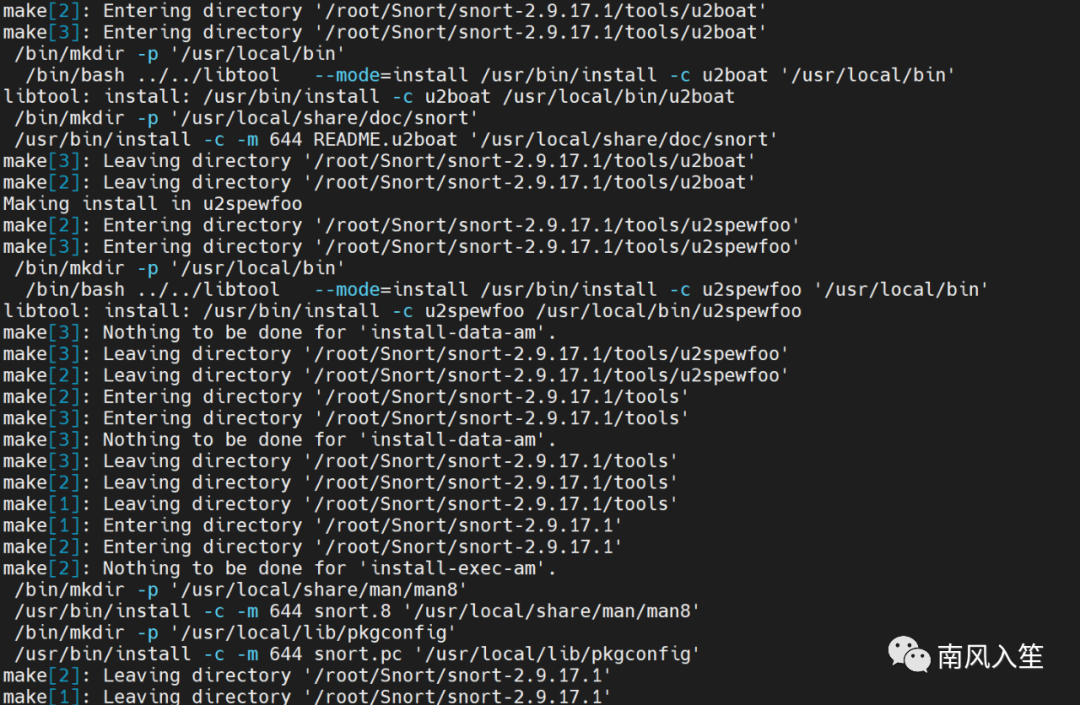
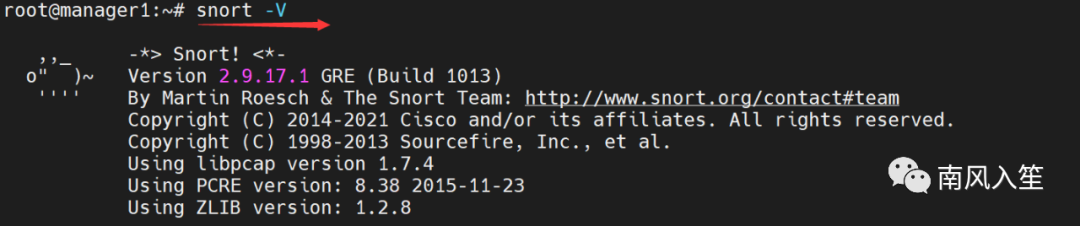
三. 解压安装DAQ和SNORT

四. 修复链接并测试
sudo ldconfig
五. 创建用户环境
# 创建用户和用户组:sudo groupadd snortsudo useradd snort -r -s sbin/nologin -c SNORT_IDS -g snort# 创建snort目录:sudo mkdir etc/snortsudo mkdir etc/snort/rulessudo mkdir etc/snort/rules/iplistssudo mkdir /etc/snort/preproc_rulessudo mkdir /usr/local/lib/snort_dynamicrulessudo mkdir /etc/snort/so_rules# 创建规则:sudo touch /etc/snort/rules/iplists/black_list.rulessudo touch /etc/snort/rules/iplists/white_list.rulessudo touch /etc/snort/rules/local.rulessudo touch /etc/snort/sid-msg.map# 创建日志目录:sudo mkdir /var/log/snortsudo mkdir /var/log/snort/archived_logs# 加权限:sudo chmod -R 775 /etc/snortsudo chmod -R 775 /var/log/snortsudo chmod -R 775 /var/log/snort/archived_logssudo chmod -R 775 /etc/snort/so_rulessudo chmod -R 775 /usr/local/lib/snort_dynamicrules# 修改文件所属用户及用户组:sudo chown -R snort:snort /etc/snortsudo chown -R snort:snort /var/log/snortsudo chown -R snort:snort /usr/local/lib/snort_dynamicrules
六. 复制配置文件
cd ~/snort-2.9.17.1/etc/sudo cp *.conf* /etc/snortsudo cp *.map /etc/snortsudo cp *.dtd /etc/snortcd ~/snort-2.9.17.1/src/dynamic-preprocessors/build/usr/local/lib/snort_dynamicpreprocessor/sudo cp * /usr/local/lib/snort_dynamicpreprocessor/
七. 注释掉snort.conf中引用的规则文件,使用PulledPork管理规则集
sudo sed -i "s/include \$RULE\_PATH/#include \$RULE\_PATH/" /etc/snort/snort.conf
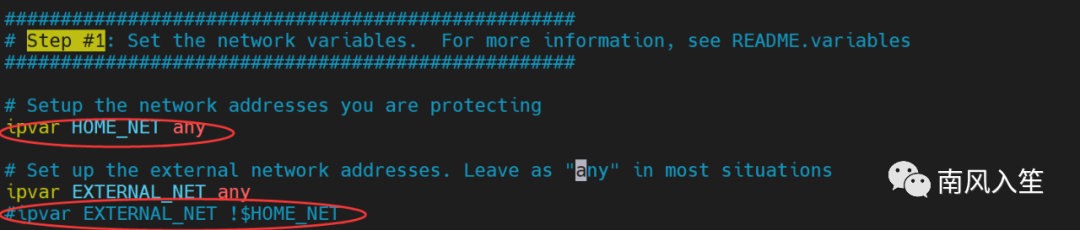
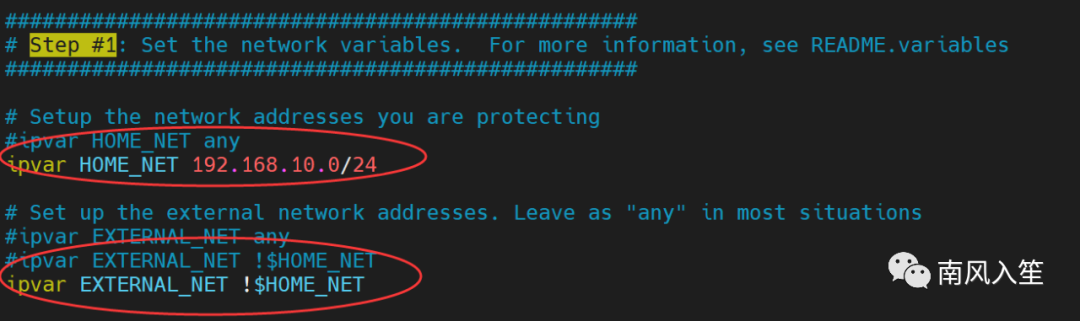
八. 修改配置文件
sudo vi /etc/snort/snort.conf#第45行,ipvar HOME_NET修改为本机的内部网络ipvar HOME_NET 192.168.10.0/24#第104行,设置以下配置文件路径var RULE_PATH /etc/snort/rulesvar SO_RULE_PATH /etc/snort/so_rulesvar PREPROC_RULE_PATH /etc/snort/preproc_rulesvar WHITE_LIST_PATH /etc/snort/rules/iplistsvar BLACK_LIST_PATH /etc/snort/rules/iplists#第521行添加# output unified2: filename merged.log, l imit 128, nostamp, mpls event types, vlan event types }output unified2: filename snort.u2, limit 128#第546行取消注释,启用local.rules文件include $RULE_PATH/local.rules
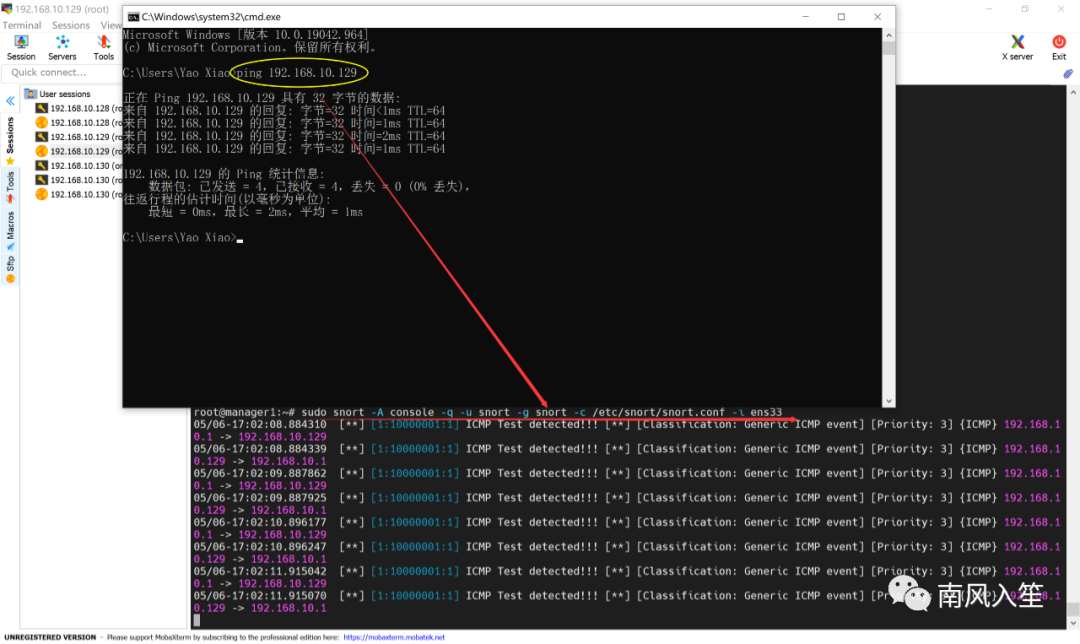
九. 添加本地规则
sudo vi /etc/snort/rules/local.rulesalert icmp any any -> $HOME_NET any (msg:"ICMP Test detected!!!"; classtype:icmp-event; sid:10000001; rev:001; GID:1; )
sudo vi /etc/snort/sid-msg.map#v21 || 10000001 || 001 || icmp-event || 0 || ICMP Test detected || url,tools.ietf.org/html/rfc792
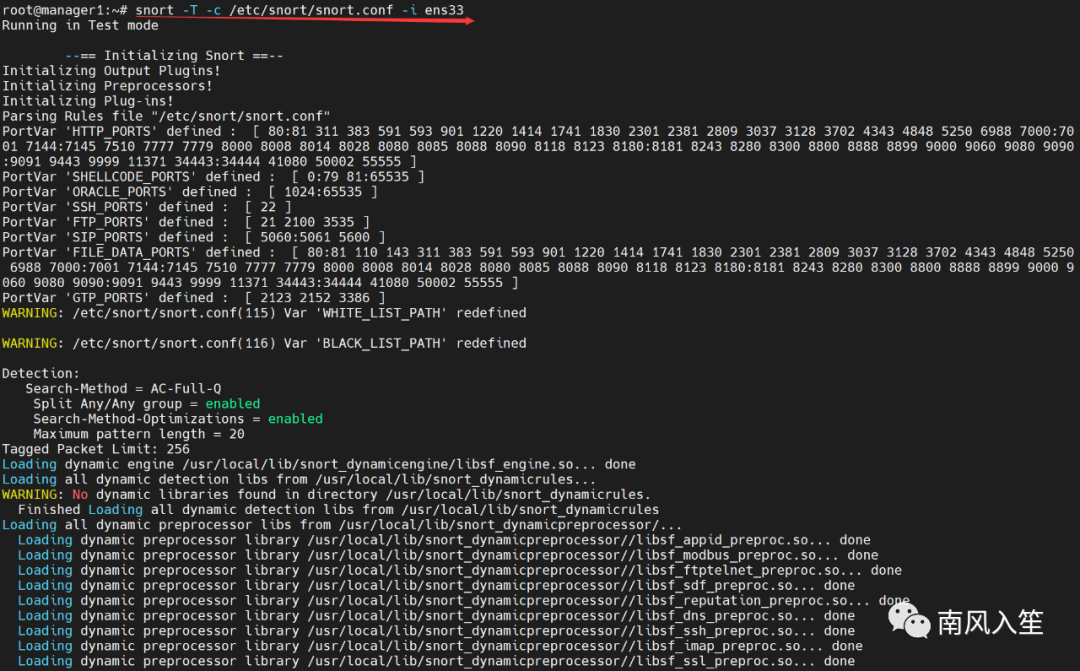
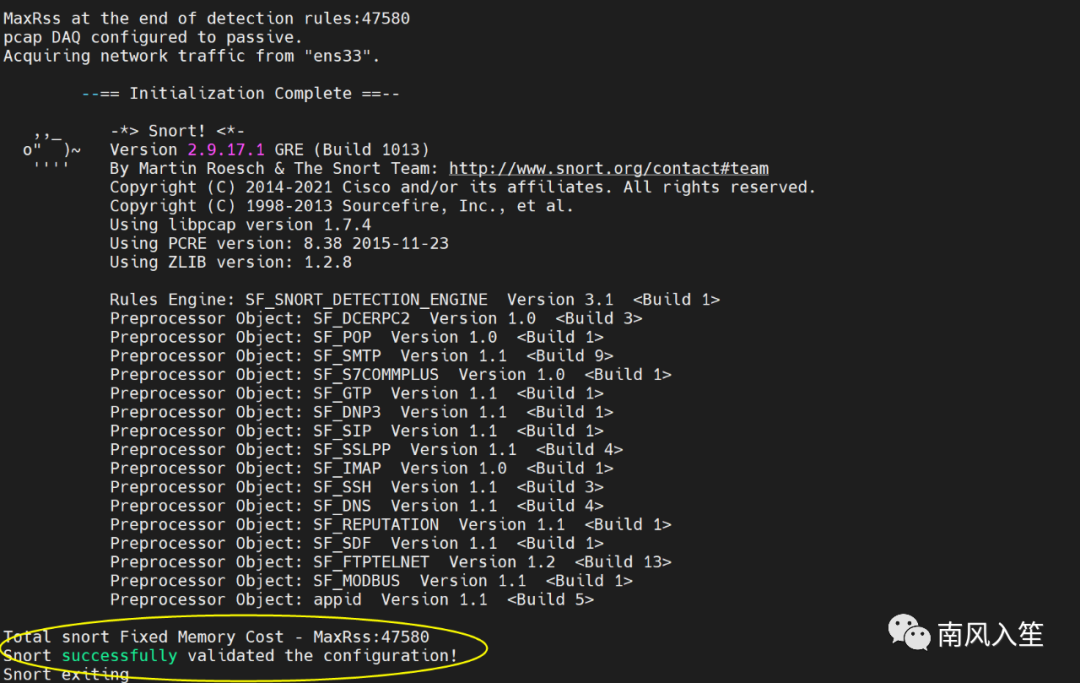
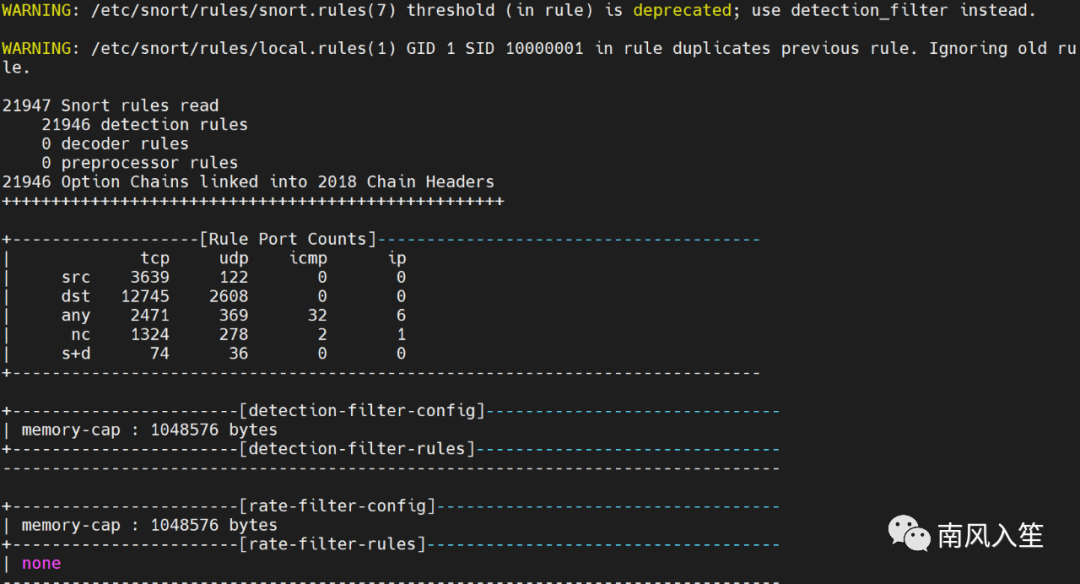
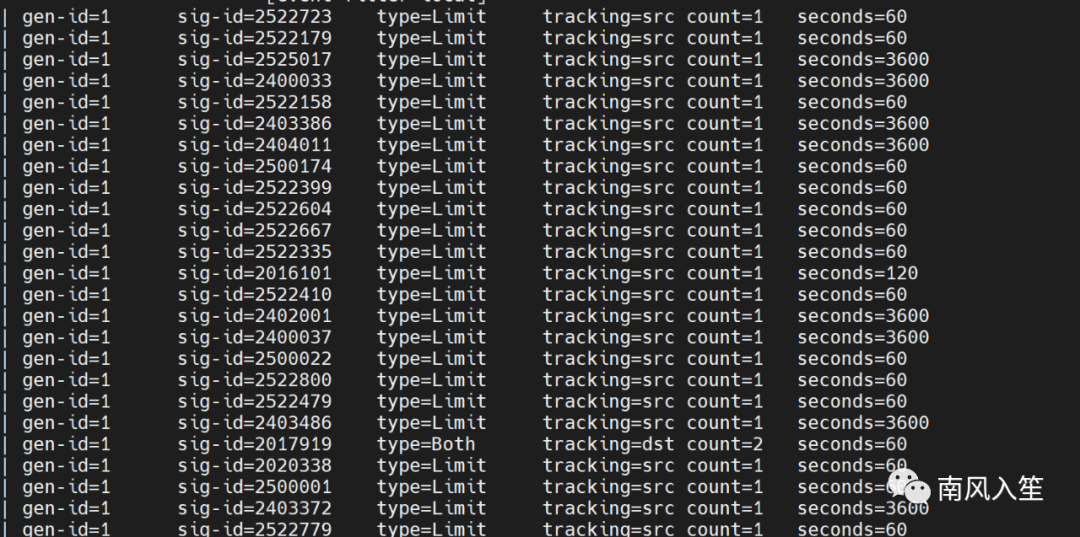
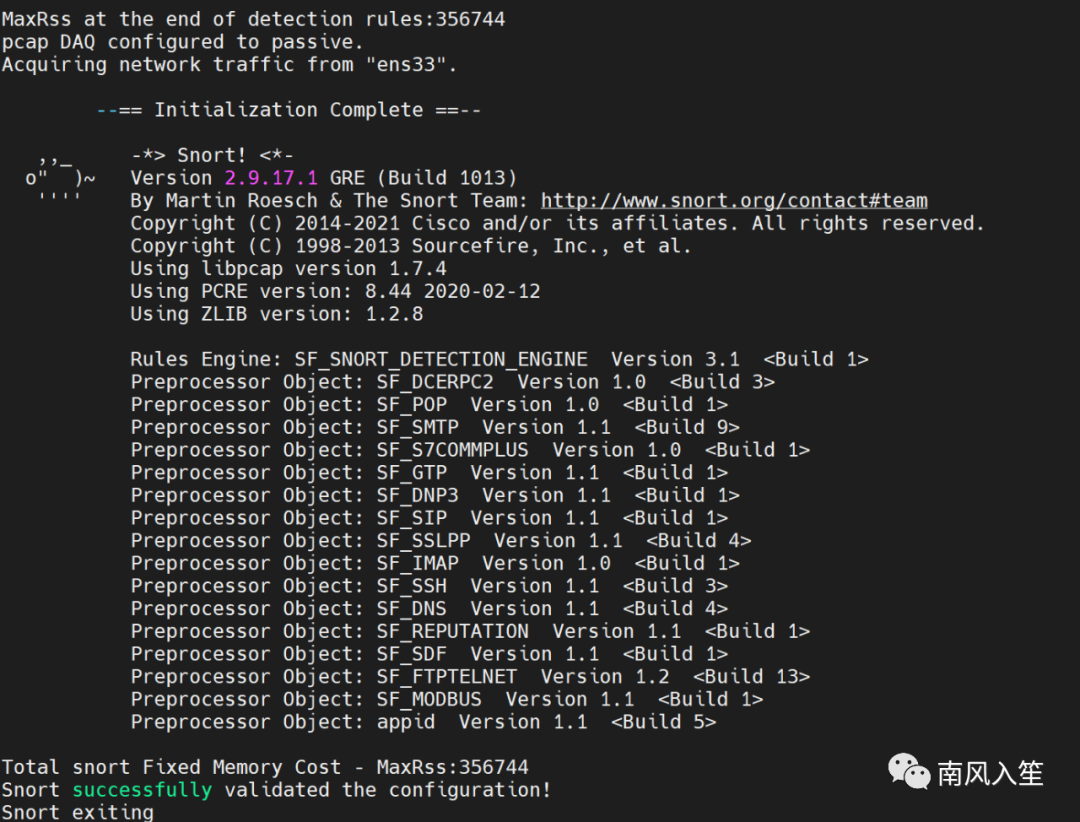
十. 测试配置文件
sudo snort -T -c /etc/snort/snort.conf -i ens33(自己网卡名)
测试功能:sudo snort -A console -q -u snort -g snort -c /etc/snort/snort.conf -i ens33
十一. 解压安装Barnyard2并测试
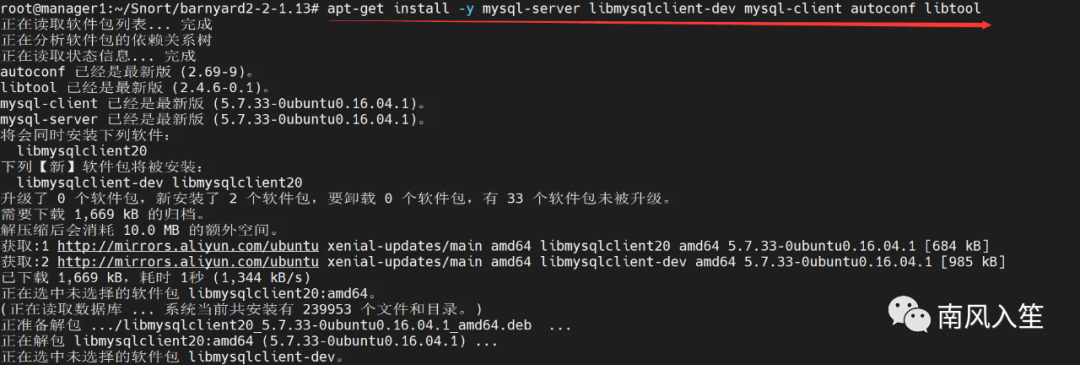
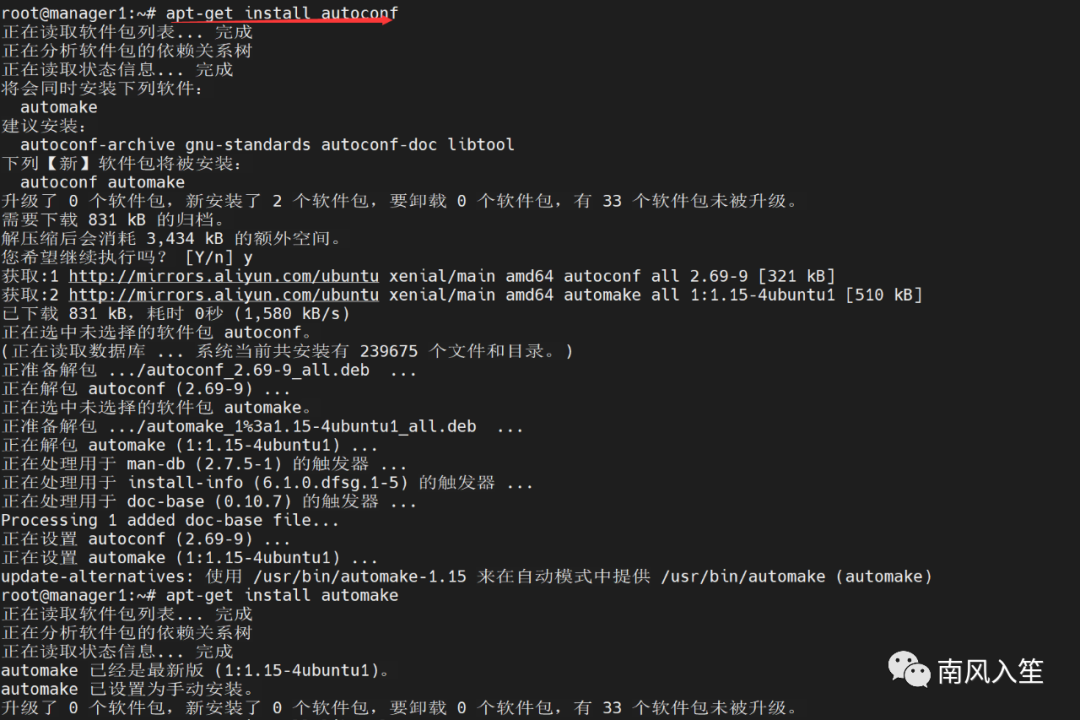
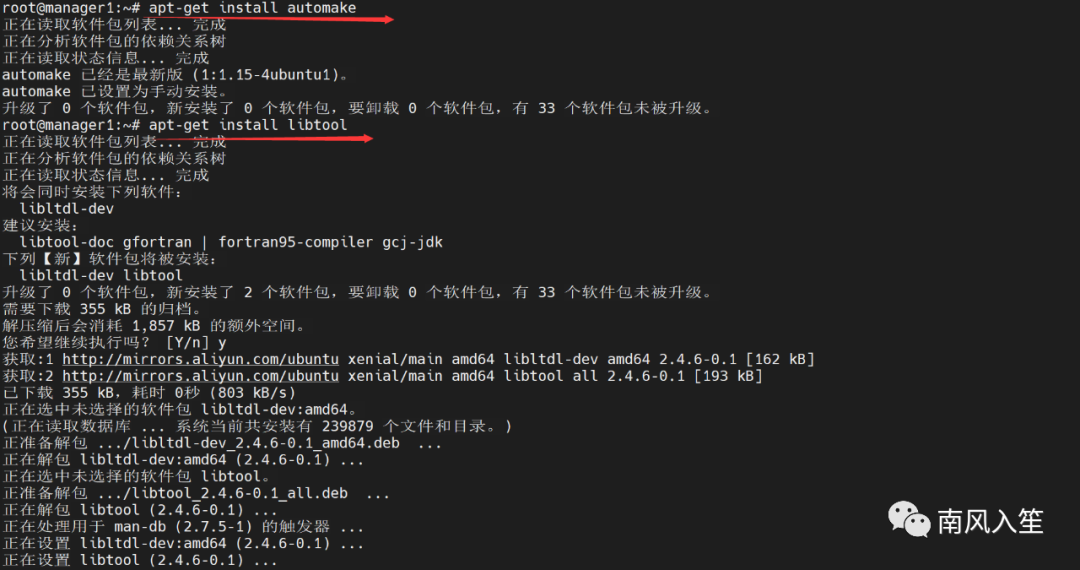
安装mysql:sudo apt-get install -y mysql-server libmysqlclient-dev mysql-client autoconf libtool
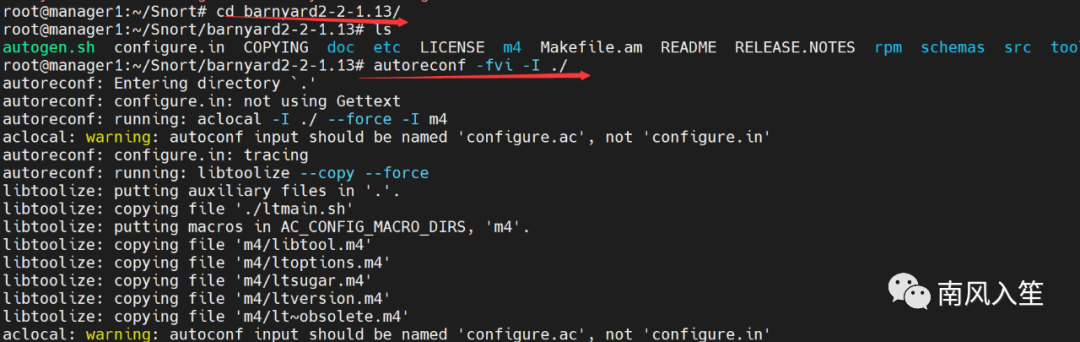
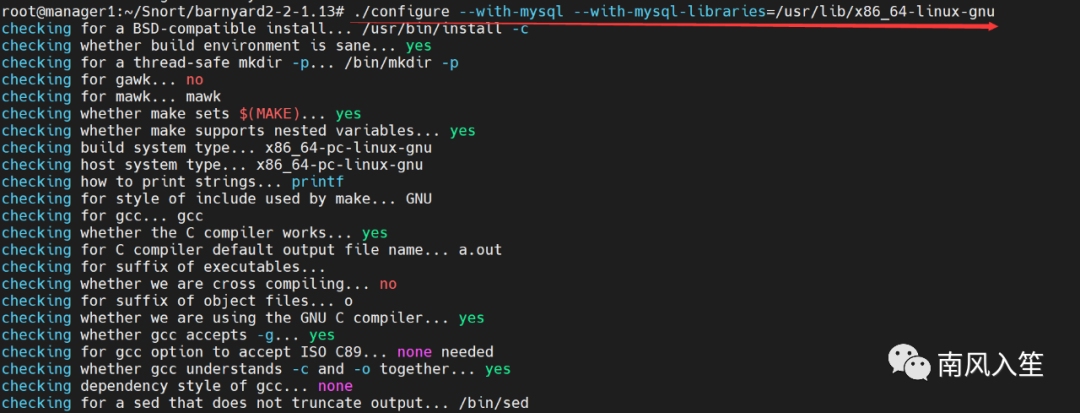
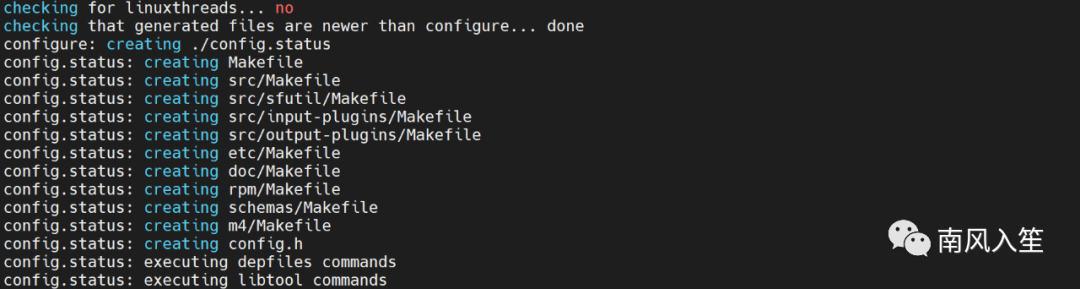
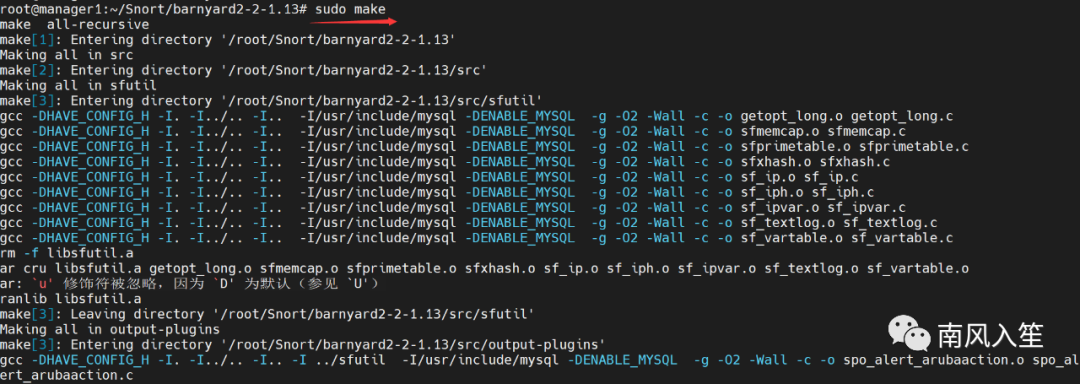
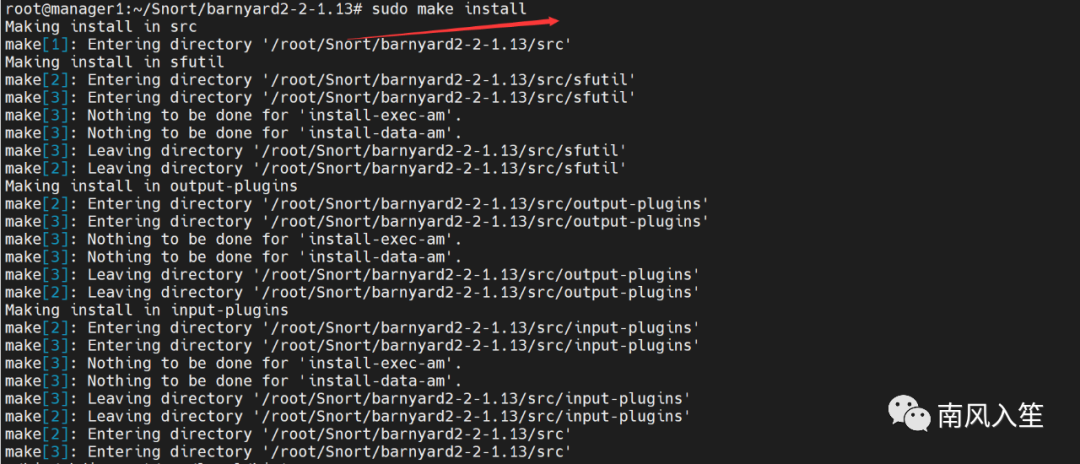
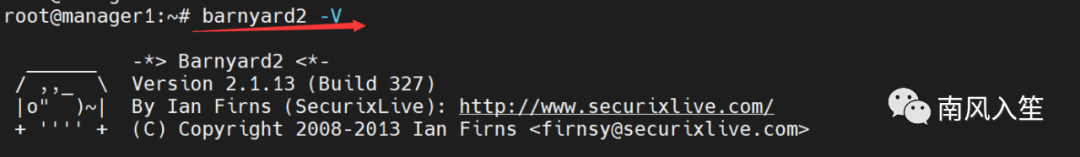
tar zxvf barnyard2-2-1.13.tar.gzcd barnyard2-2-1.13autoreconf -fvi -I ././configure --with-mysql --with-mysql-libraries=/usr/lib/x86_64-linux-gnusudo makesudo make install
十二. 修改配置文件并配置数据库
设置配置文件:sudo cp ~/barnyard2-2-1.13/etc/barnyard2.conf /etc/snort/sudo mkdir /var/log/barnyard2sudo chown snort.snort /var/log/barnyard2sudo touch /var/log/snort/barnyard2.waldosudo chown snort.snort /var/log/snort/barnyard2.waldo

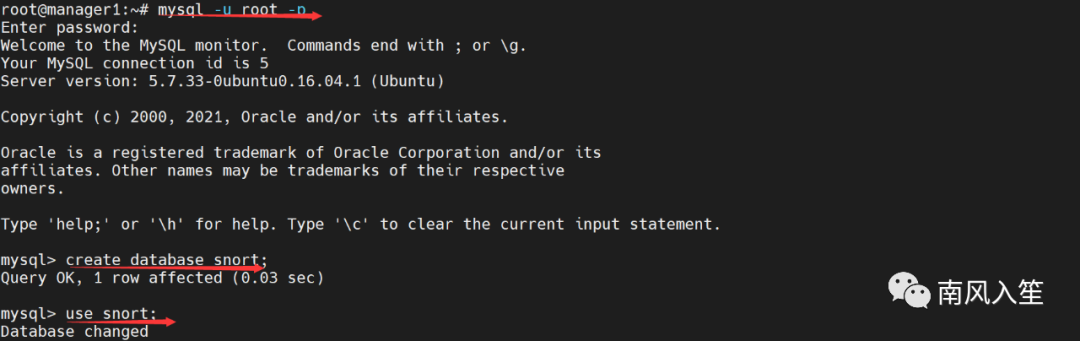
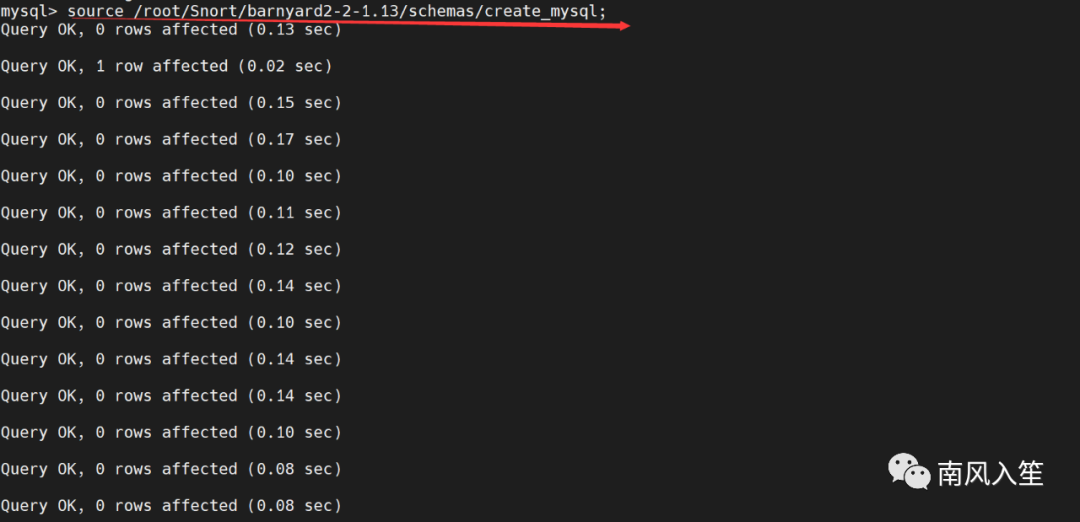
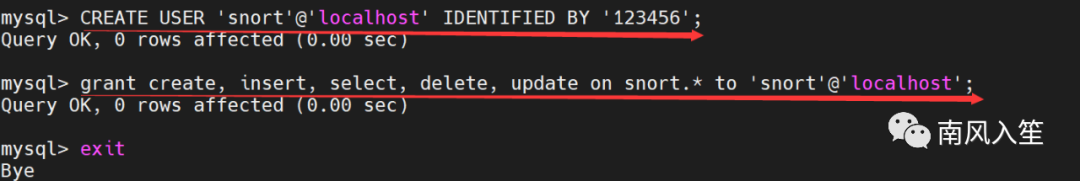
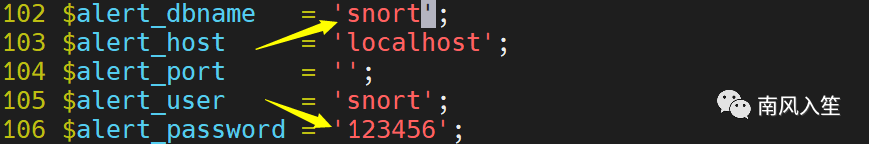
配置数据库,密码为自己设置的,存储文件的位置自己设定:ubuntu@ubuntu:~$ mysql -u root -pmysql> create database snort;mysql> use snort;mysql> source /root/Snort/barnyard2-2-1.13/schemas/create_mysql;mysql> CREATE USER 'snort'@'localhost' IDENTIFIED BY '123456';mysql> grant create, insert, select, delete, update on snort.* to 'snort'@'localhost';mysql> exit;

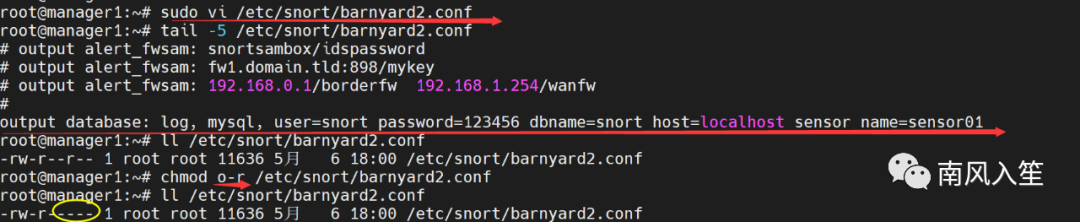
添加数据库配置:sudo vi /etc/snort/barnyard2.conf#在末尾添加数据库配置output database: log, mysql, user=snort password=123456 dbname=snort host=localhost sensor name=sensor01
修改barnyard2.conf权限防止被修改:sudo chmod o-r /etc/snort/barnyard2.conf
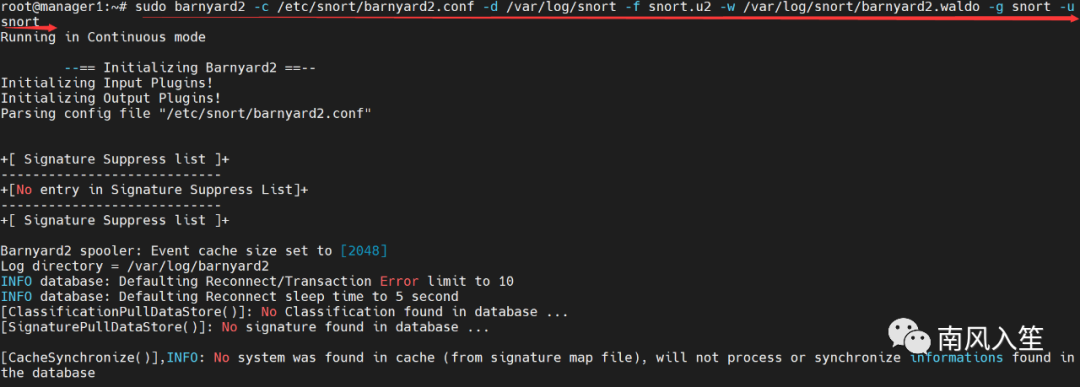
测试:# 连续处理模式,设置barnyard2.waldo为书签sudo barnyard2 -c /etc/snort/barnyard2.conf -d /var/log/snort -f snort.u2 -w /var/log/snort/barnyard2.waldo -g snort -u snort
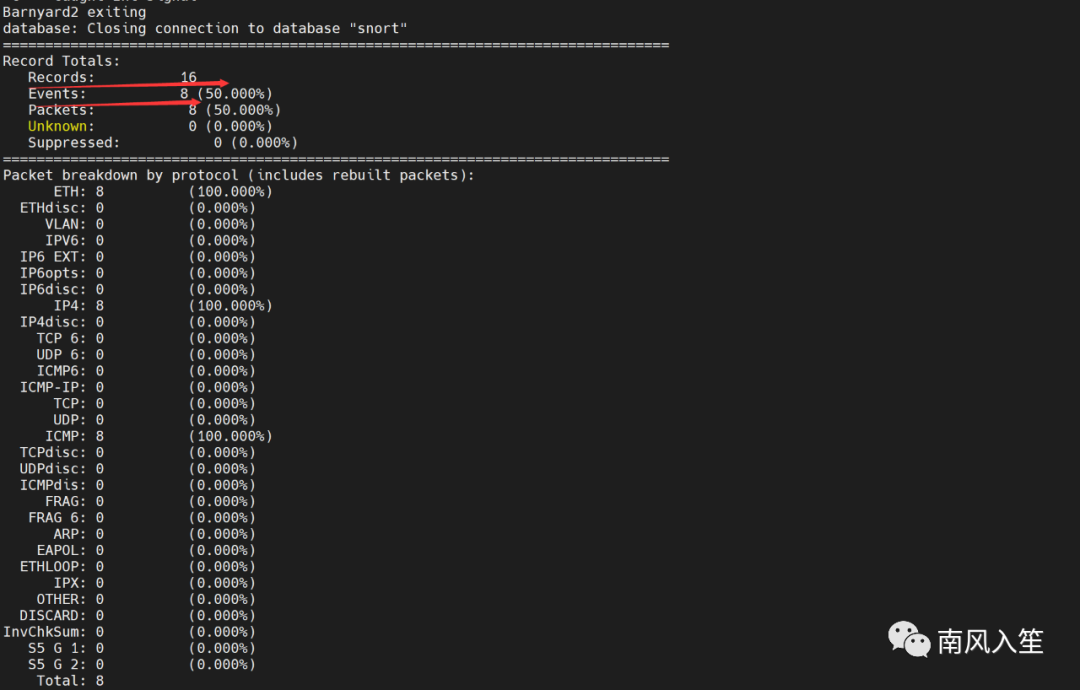
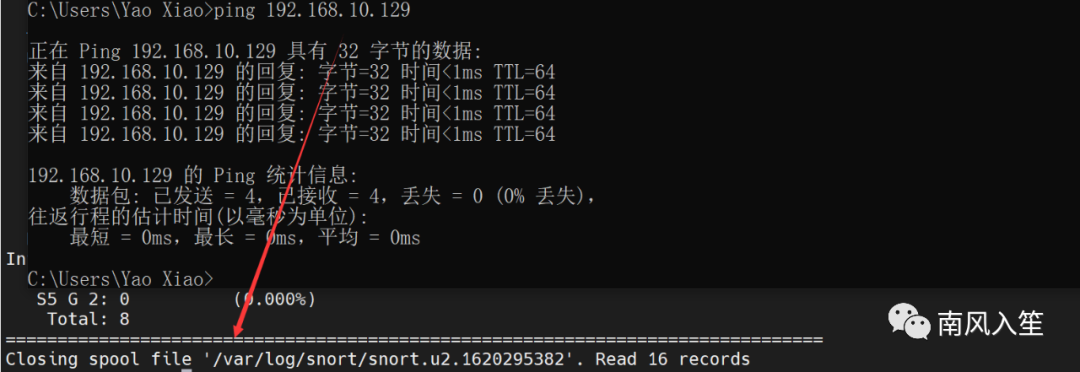
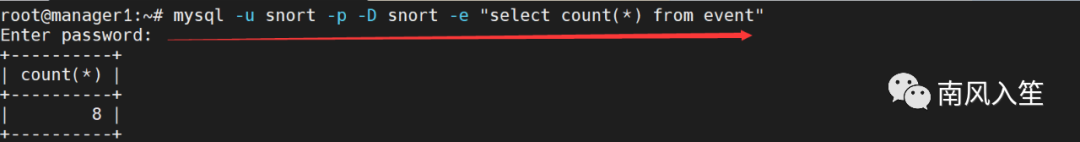
# 查看数据库条目数量,看是否增加mysql -u snort -p -D snort -e "select count(*) from event"
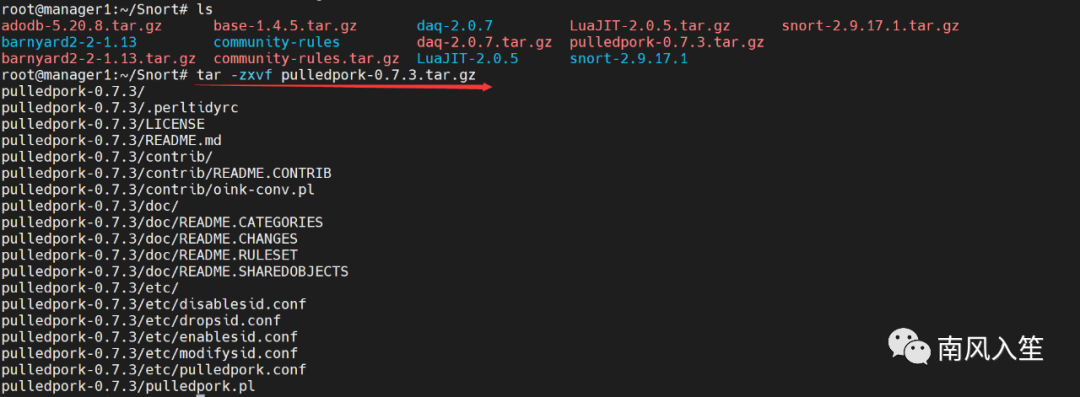
十三. 解压安装Pulledpork并测试
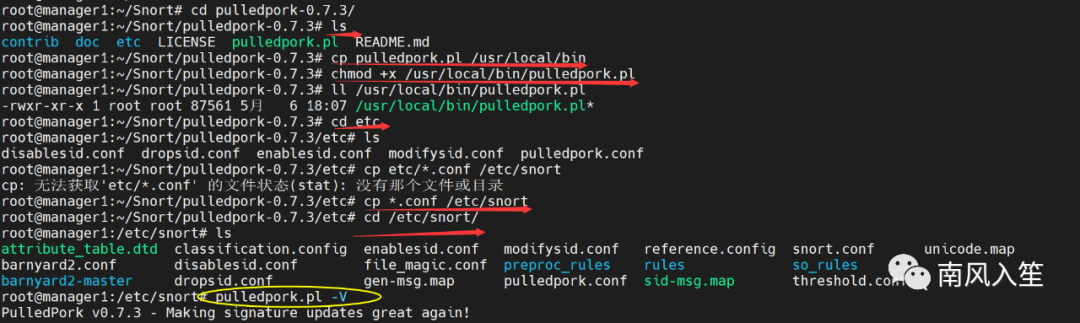
解压配置:tar xzvf pulledpork-v0.7.3.tar.gzcd pulledpork-v0.7.3/sudo cp pulledpork.pl /usr/local/binsudo chmod +x /usr/local/bin/pulledpork.plsudo cp etc/*.conf /etc/snort
测试:ubuntu@ubuntu:~$ pulledpork.pl -VPulledPork v0.7.3 - Making signature updates great again!
十四. 修改配置文件并更新测试规则
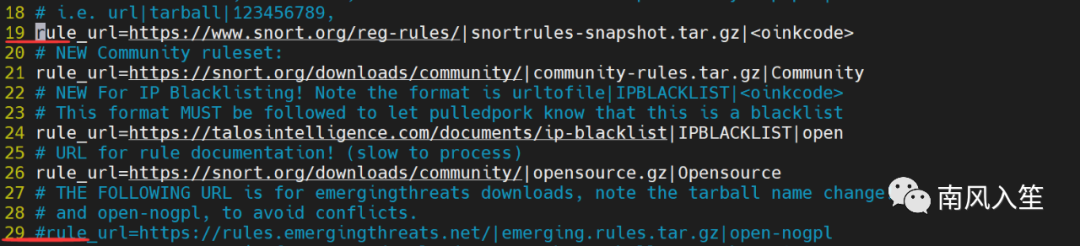
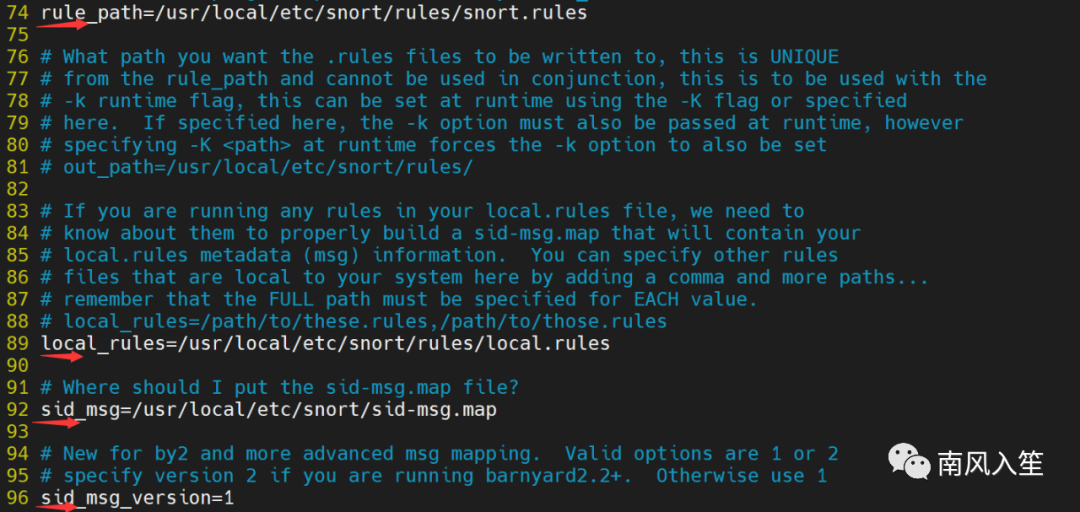
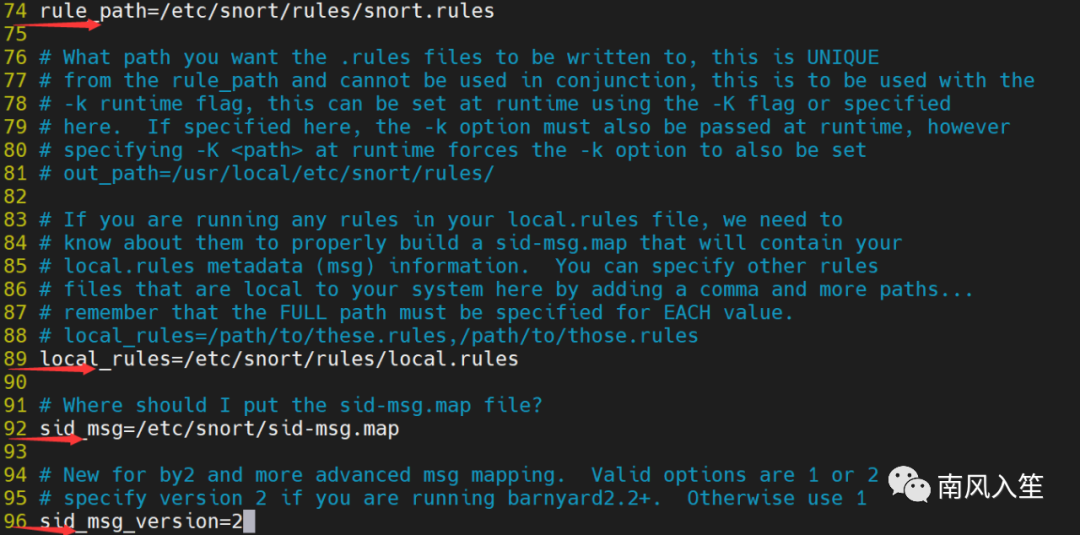
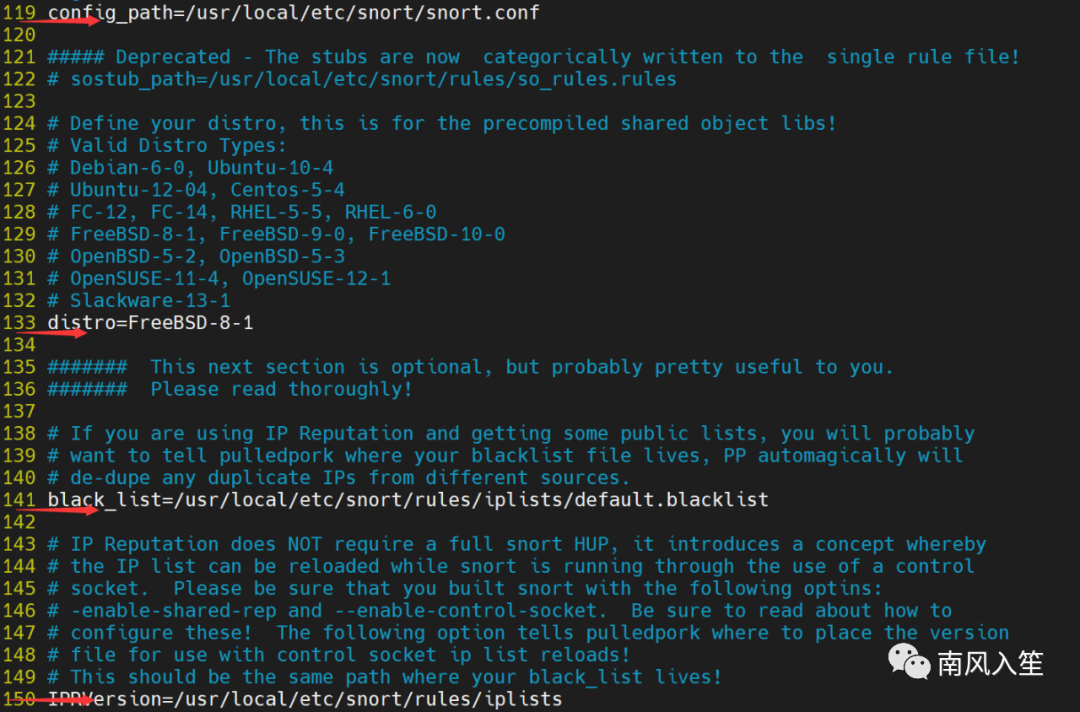
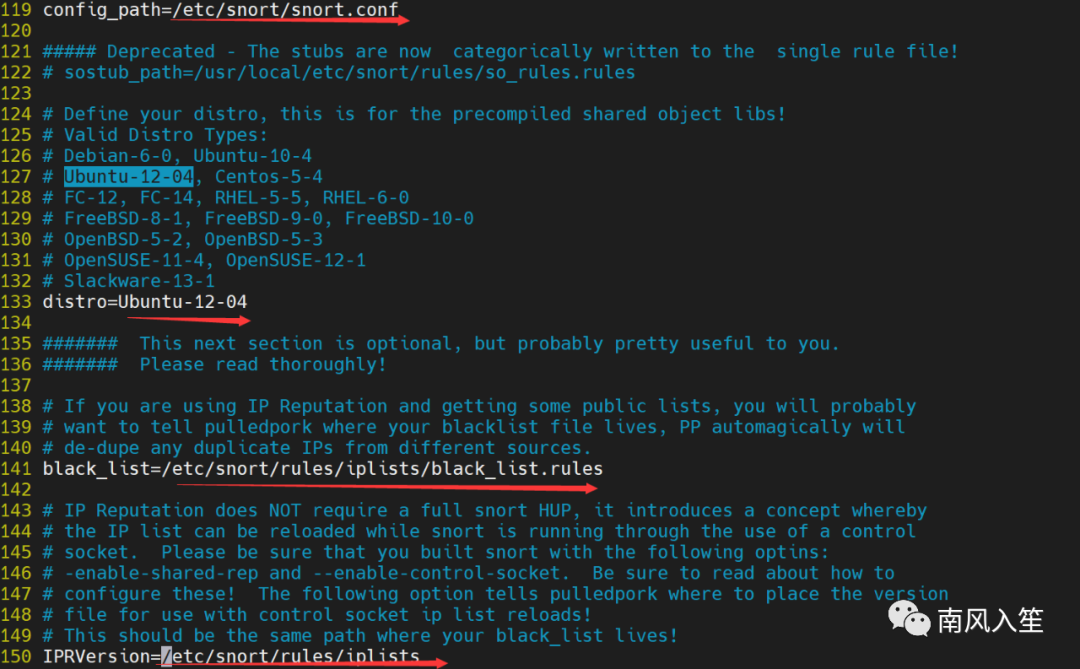
sudo vi /etc/snort/pulledpork.conf#第19行:输入注册账户生成的oinkcode,若没有则注释掉#第29行:取消注释可下载针对新兴威胁的规则#第74行:更改为:rule_path = /etc/snort/rules/snort.rules#第89行:更改为:local_rules = /etc/snort/rules/local.rules#第92行:更改为:sid_msg = /etc/snort/sid-msg.map#第96行:更改为:sid_msg_version = 2#第119行:更改为:config_path = /etc/snort/snort.conf#第133行:更改为:distro = Ubuntu-12-04#第141行:更改为:black_list = /etc/snort/rules/iplists/black_list.rules#第150行:更改为:IPRVersion = /etc/snort/rules/iplists

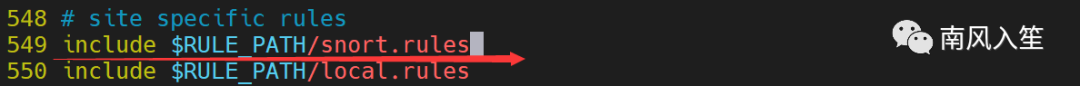
sudo vi /etc/snort/snort.conf#第548行添加include $RULE_PATH/snort.rules
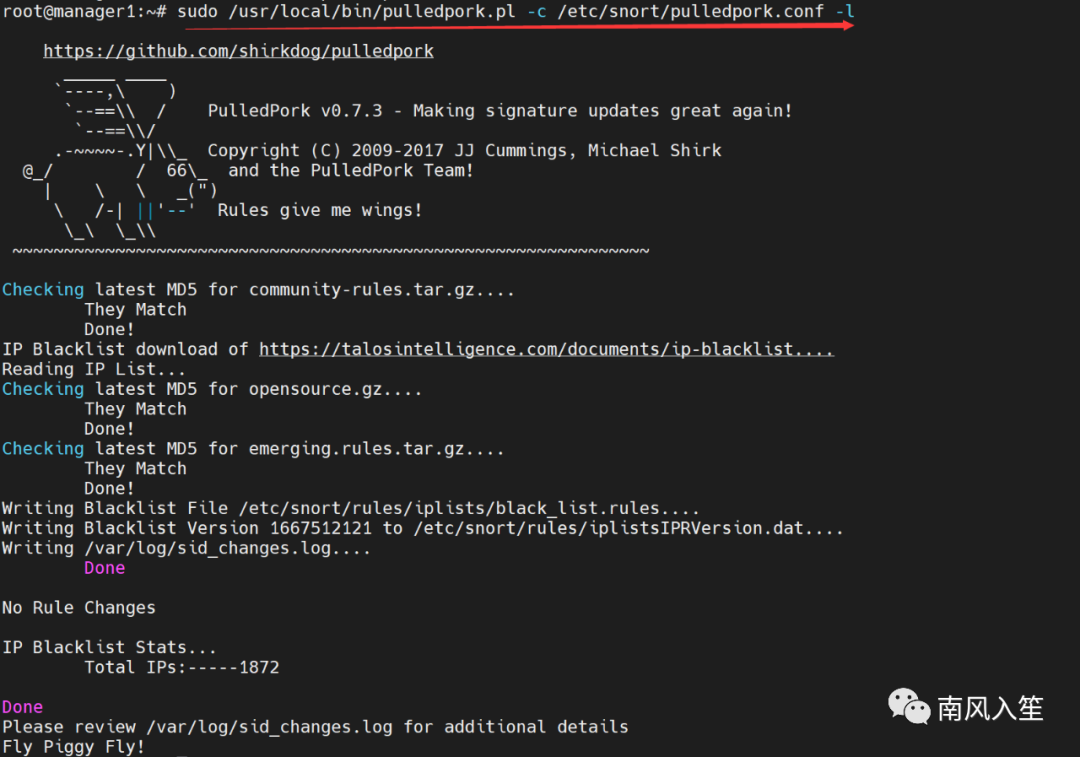
更新规则:sudo /usr/local/bin/pulledpork.pl -c /etc/snort/pulledpork.conf -l
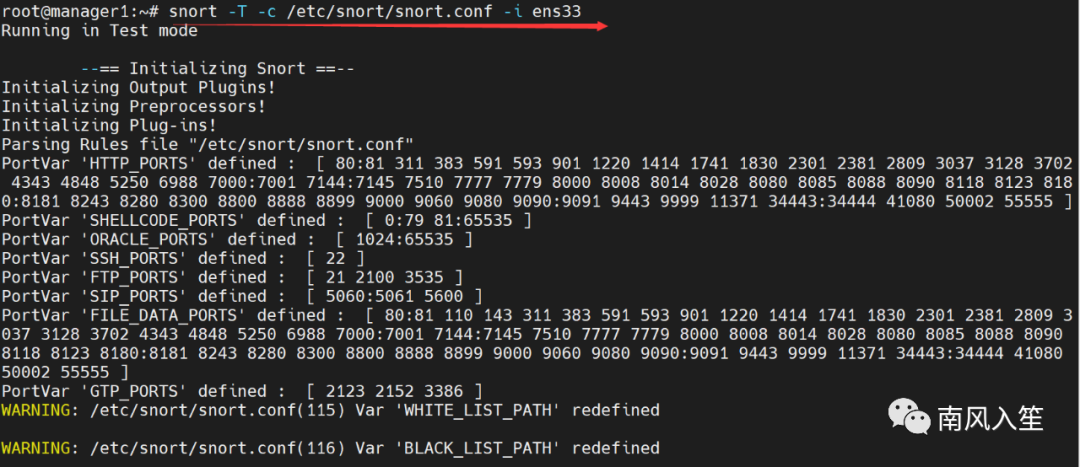
测试规则:sudo snort -T -c /etc/snort/snort.conf -i ens33
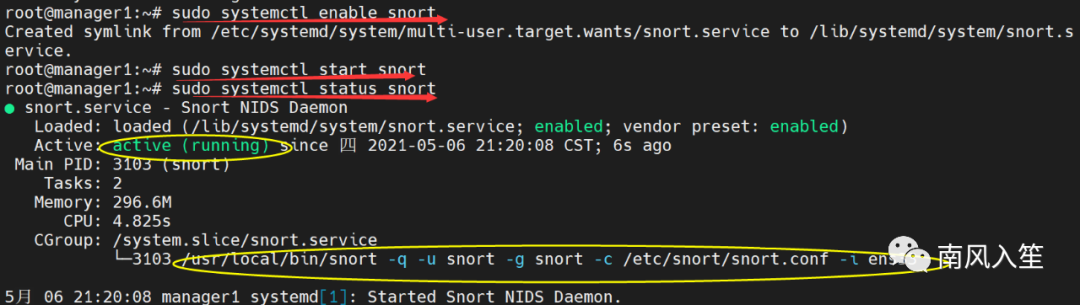
十五. 创建服务
#创建snort服务配置文件sudo vi /lib/systemd/system/snort.service[Unit]Description=Snort NIDS DaemonAfter=syslog.target network.target[Service]Type=simpleRestart=alwaysExecStart=/usr/local/bin/snort -q -u snort -g snort -c /etc/snort/snort.conf -i ens33[Install]WantedBy=multi-user.target
#设置开机启动sudo systemctl enable snort#启动服务sudo systemctl start snort#检查服务状态sudo systemctl status snort

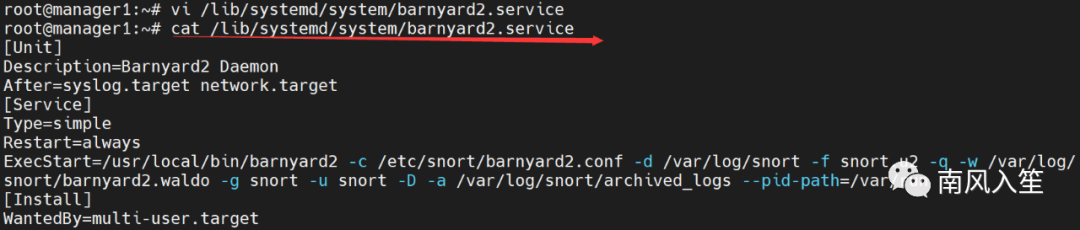
#创建Barnyard2服务配置文件sudo vi /lib/systemd/system/barnyard2.service[Unit]Description=Barnyard2 DaemonAfter=syslog.target network.target[Service]Type=simpleRestart=alwaysExecStart=/usr/local/bin/barnyard2 -c /etc/snort/barnyard2.conf -d /var/log/snort -f snort.u2 -q -w /var/log/snort/barnyard2.waldo -g snort -u snort -D -a /var/log/snort/archived_logs --pid-path=/var/run[Install]WantedBy=multi-user.target
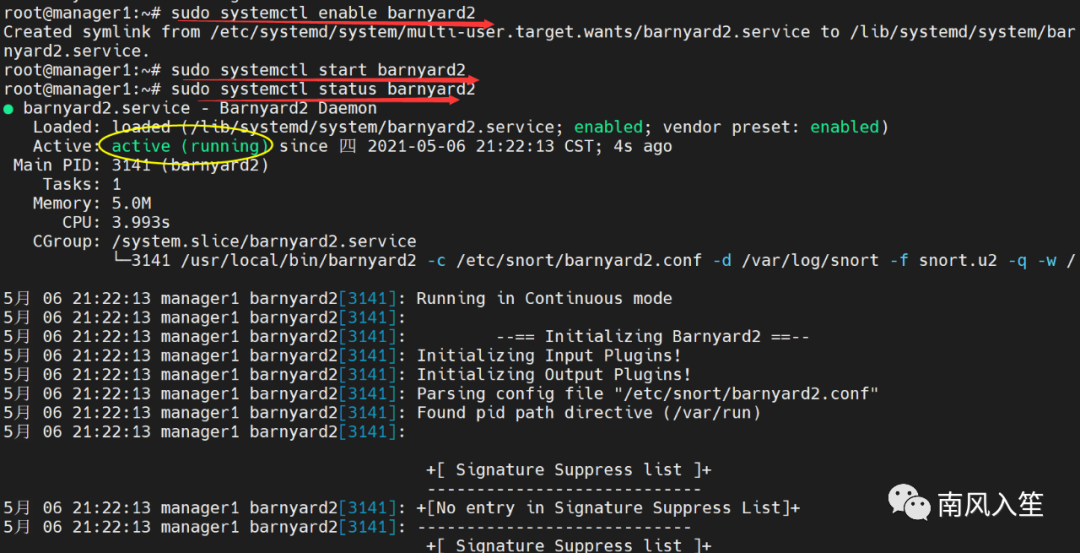
#设置开机启动sudo systemctl enable barnyard2#启动服务sudo systemctl start barnyard2#检查服务状态sudo systemctl status barnyard2
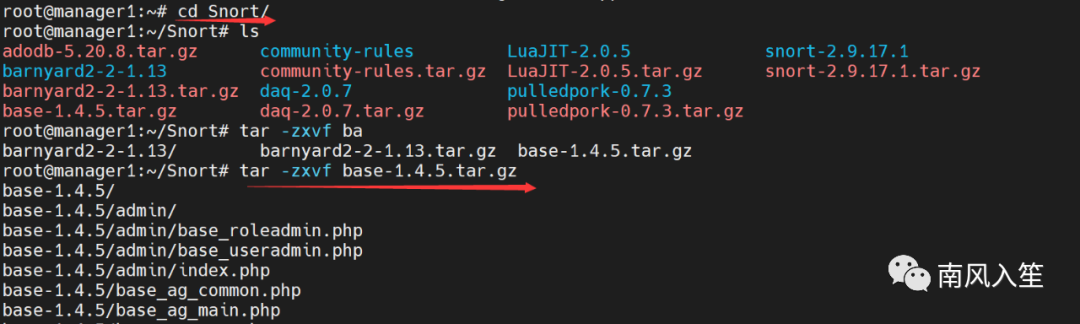
十六. 解压安装BASE并测试
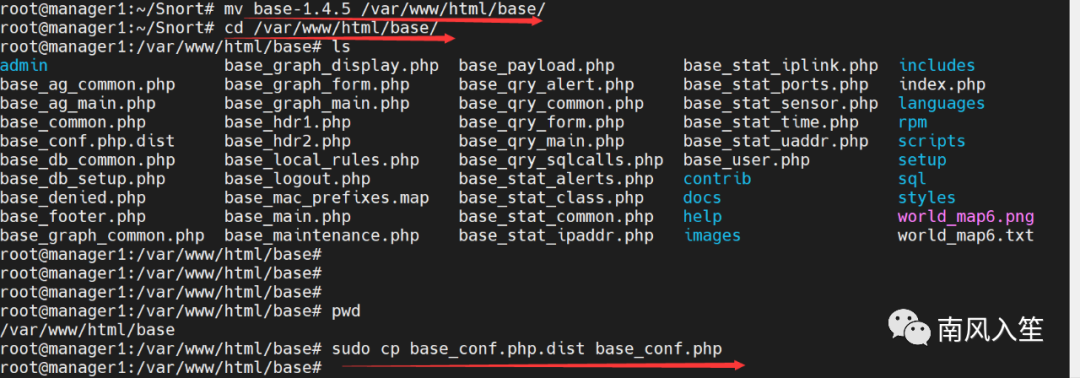
解压:tar xzvf base-1.4.5.tar.gzsudo mv base-1.4.5 /var/www/html/base/
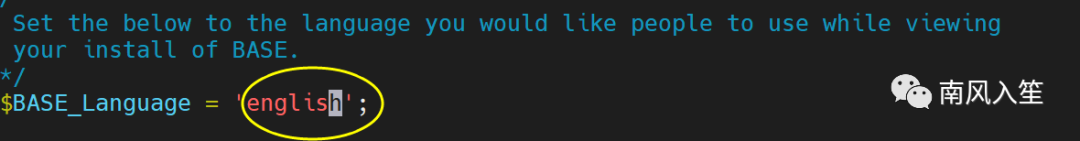
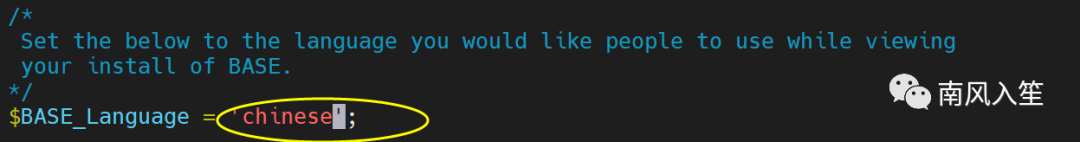
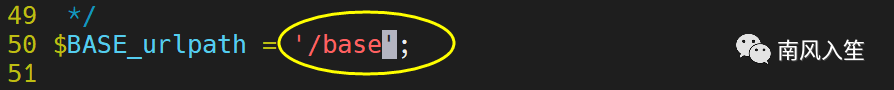
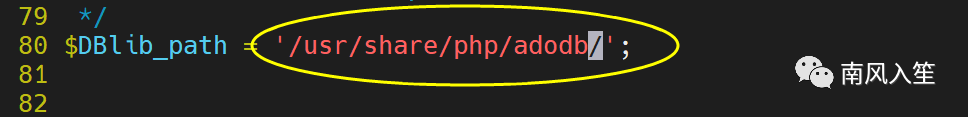
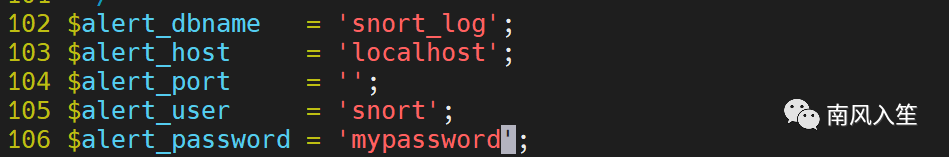
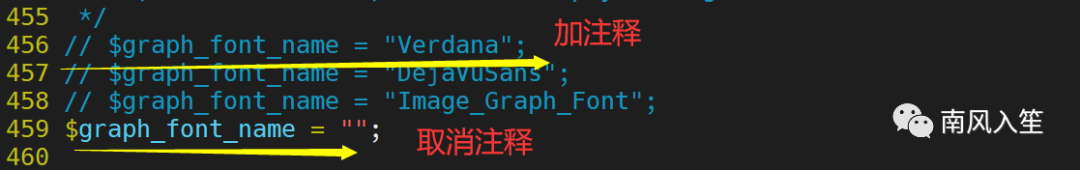
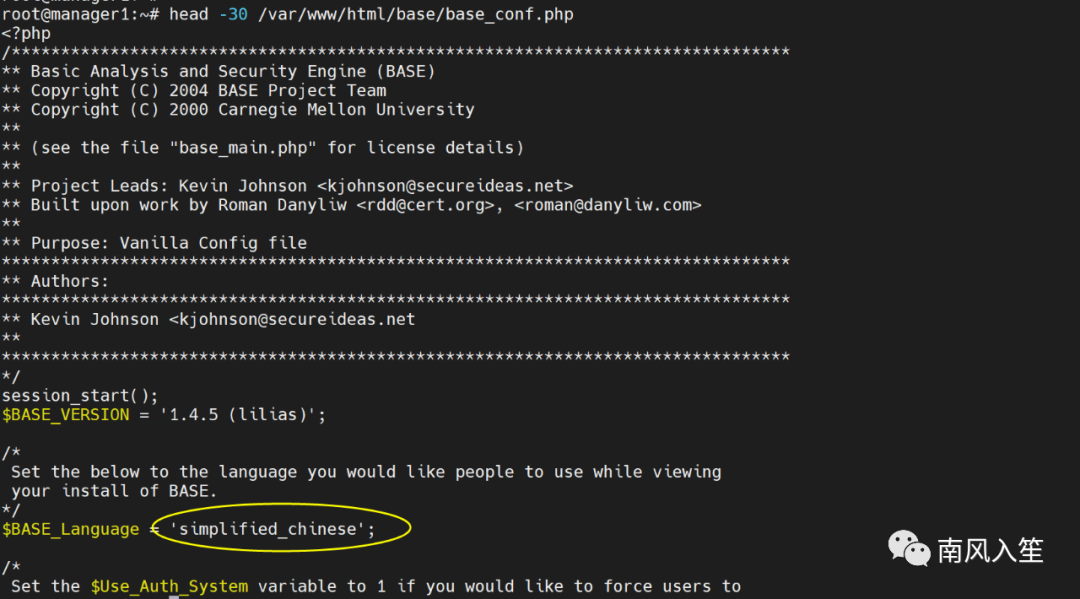
修改配置文件:cd /var/www/html/basesudo cp base_conf.php.dist base_conf.phpsudo vi /var/www/html/base/base_conf.php$BASE_Language = 'chinese'; # line 27$BASE_urlpath = '/base'; # line 50$DBlib_path = '/usr/share/php/adodb'; #line 80$alert_dbname = 'snort'; # line 102$alert_host = 'localhost';$alert_port = '';$alert_user = 'snort';$alert_password = '123456'; # line 106// $graph_font_name = "Verdana";// $graph_font_name = "DejaVuSans";// $graph_font_name = "Image_Graph_Font";$graph_font_name = "";
sudo chown -R www-data:www-data /var/www/html/basesudo chmod o-r /var/www/html/base/base_conf.phpsudo service apache2 restart
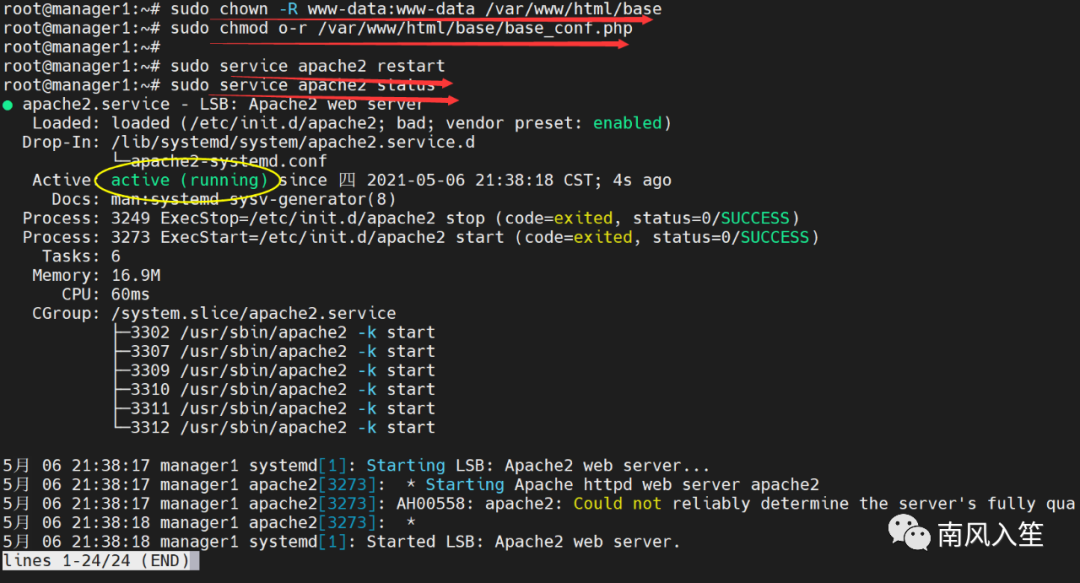
测试:http://本机虚拟机ip地址/base
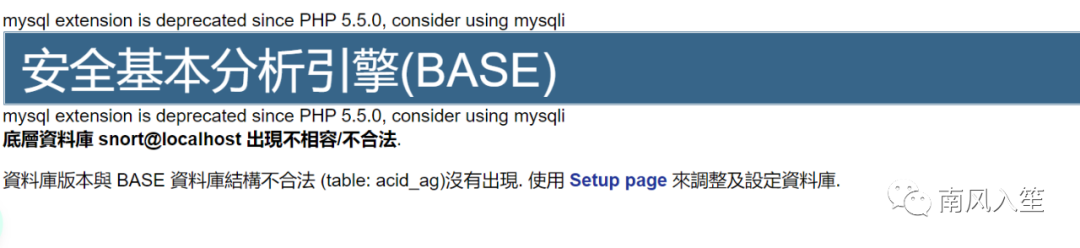
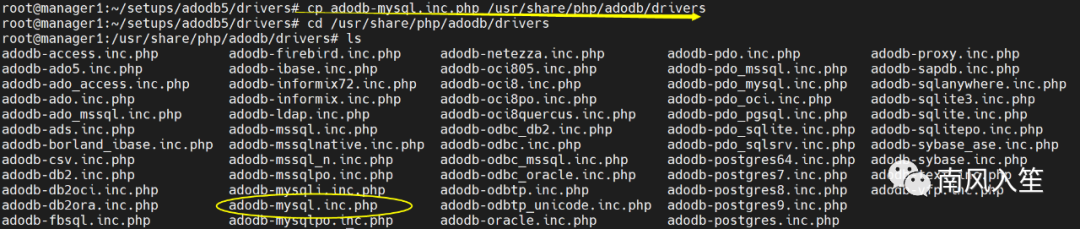
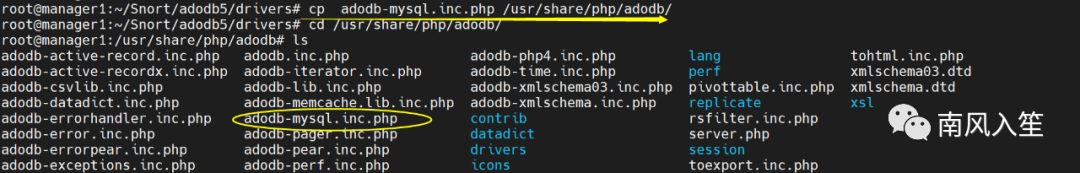
测试时发现在/usr/share/php/adodb/drivers目录下没有adodb-mysql.inc.php这个文件导致报错,之前第二步时已经下载,将其解压并将其drivers目录下的该文件拷贝到咱们到/usr/share/php/adodb这个目录下。这个图片复制时是不合适的。正确命令为:cd 您解压后adodb文件夹目录下的drivers目录下cp adodb-mysql.inc.php /usr/share/php/adodb
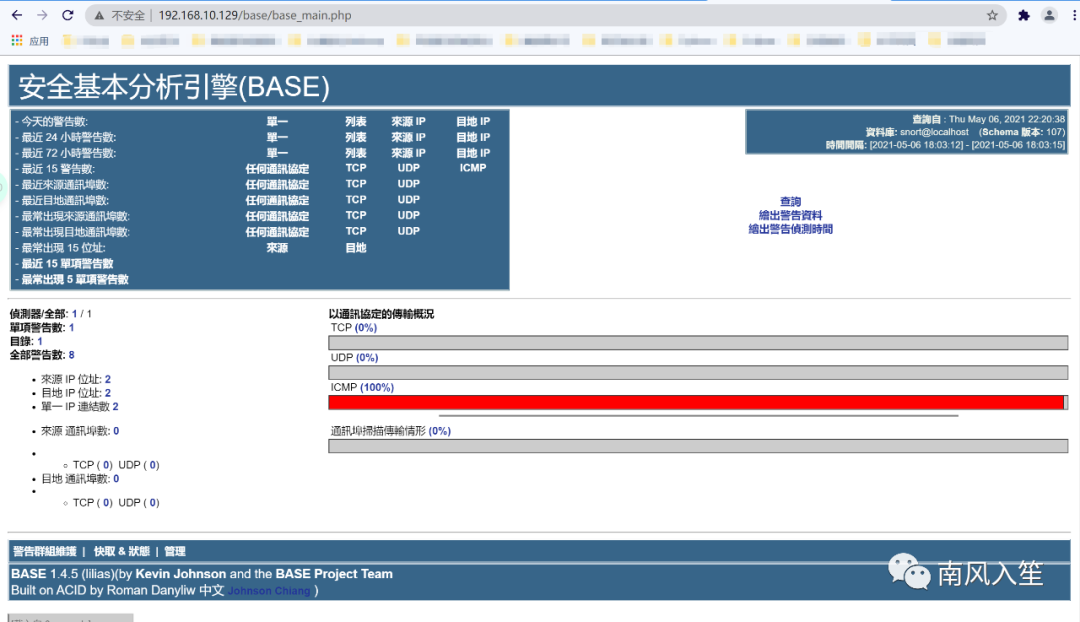
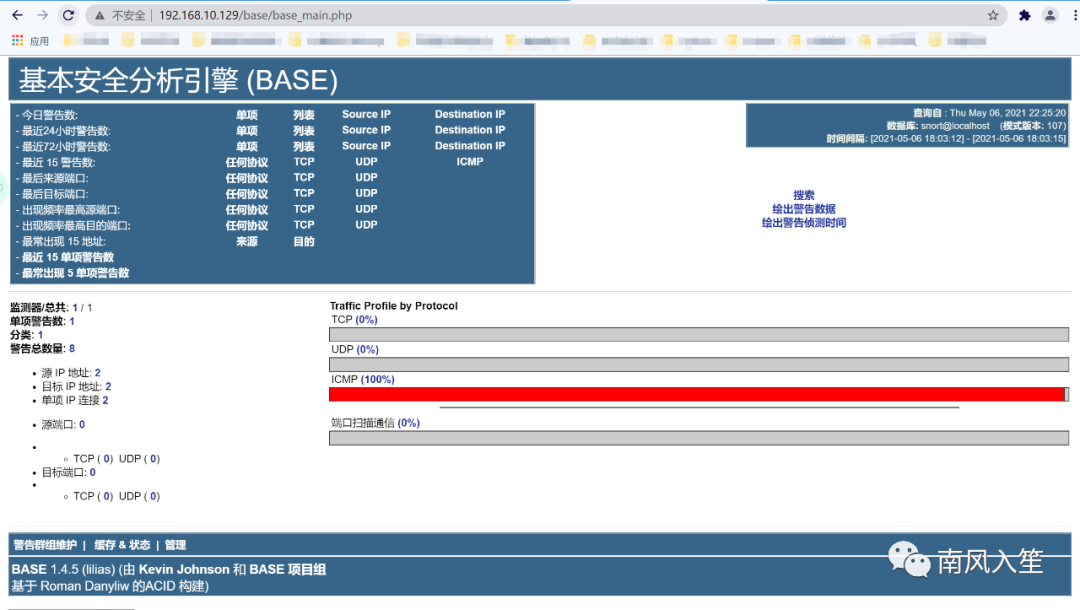
十七. Web端查看并解决相应问题
1. 字体调整简体中文。
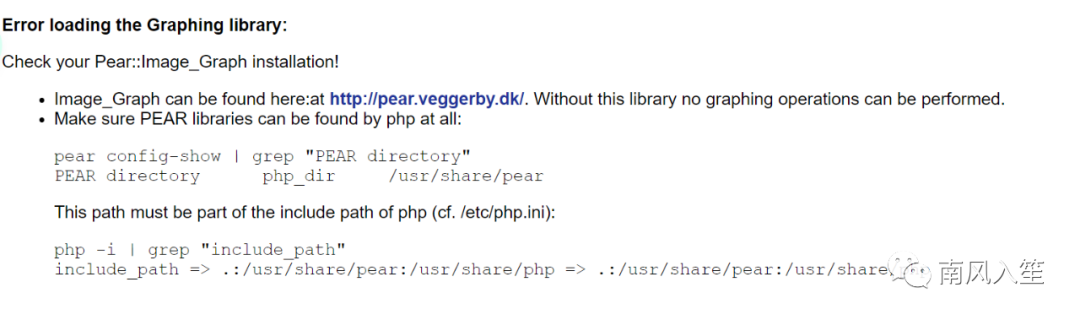
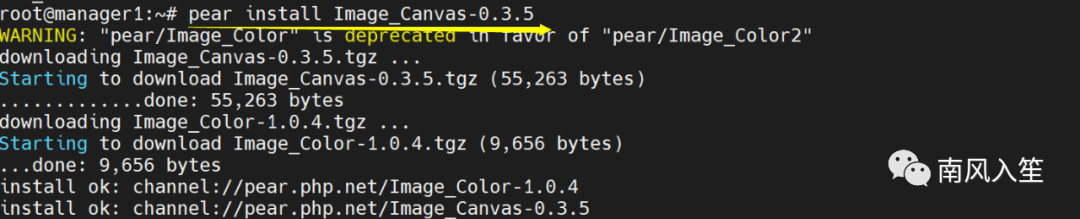
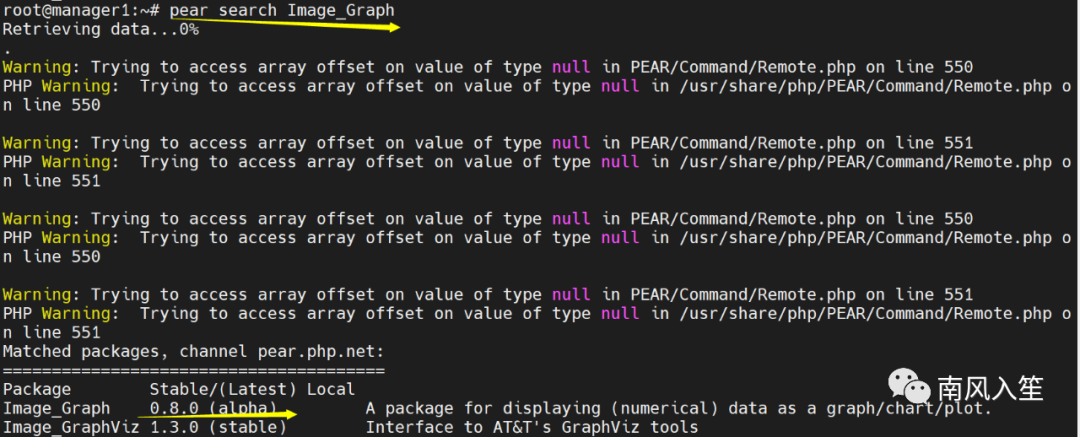
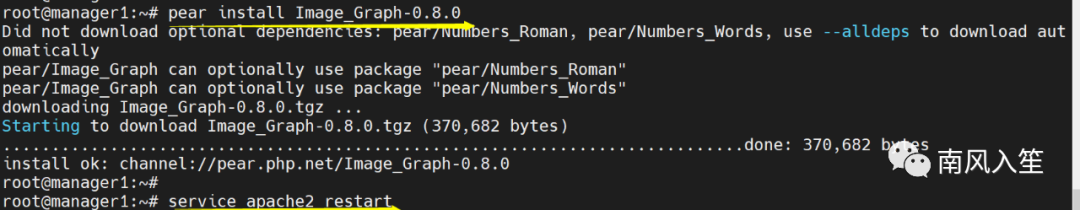
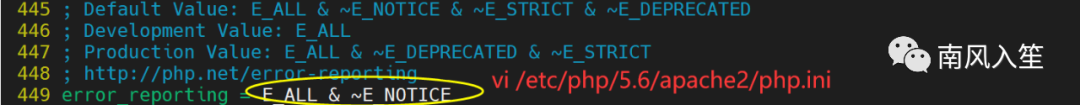
2. 解决不能加载图像库的问题,记得修改后重启服务

十八. 本地主机ping虚拟机ip地址,查看Web端
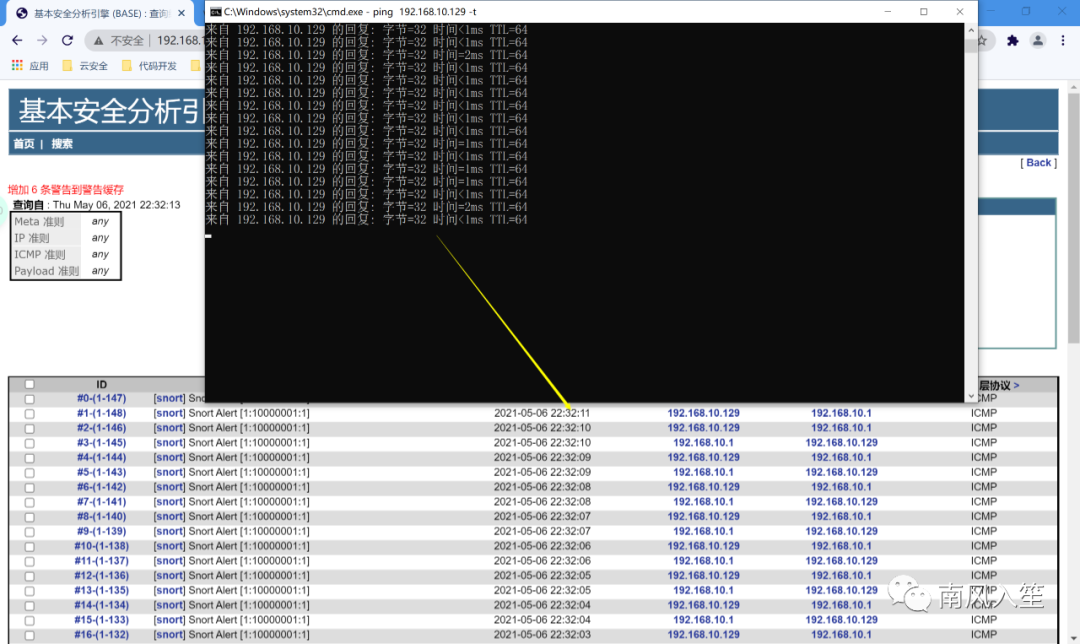
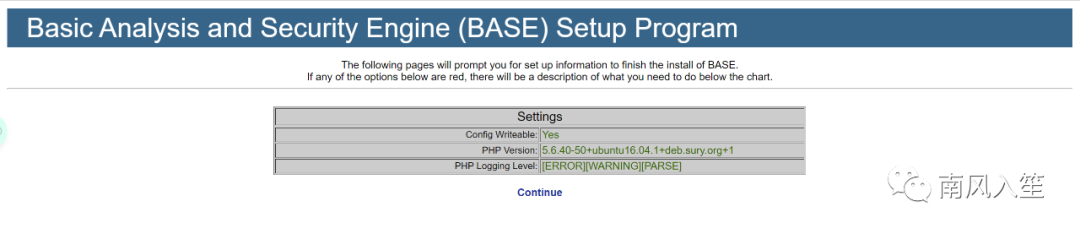
小贴士:第16步修改配置文件咱们可以也使用图形化方式配置,如下图:# 修改这个文件是因为它提示报错,如果您打开就是第二幅图这样就不用管了,直接点击Continue即可。
喜欢的小伙伴可以尝试一下哦
文章转载自南风入笙,如果涉嫌侵权,请发送邮件至:contact@modb.pro进行举报,并提供相关证据,一经查实,墨天轮将立刻删除相关内容。






